No platform is an island unto itself. Customer-ready solutions and the ability to address real use cases hinge on successful partner integrations that bring multiple technologies to bear on real-world problems.
Nozomi Networks has been able to amass one of the most robust technical alliance ecosystems in the OT/ICS security industry based on the unique value we bring, as well as the flexibility and ease of integration of our platform. In this post, we summarize some of our most recent alliance updates that cover new platforms or new features through integration.
Before we dive in, it might be good to summarize how we focus and prioritize our technology alliances so it’s a win-win for both parties. As you likely know, Nozomi Networks delivers a passive asset intelligence, vulnerability management and threat analysis solution. This has been created with OT/ICS and now IoT environments in mind. Proactive security policy enforcement can be disruptive to these critical processes and is not a specific focus of our platform. But that’s a great opportunity for us to partner for those environments that do need to enforce policies, and, in fact, can update behavior based on the security intelligence that Nozomi Networks provides. Devices like firewalls are a primary example of this integration with enforcement solutions, and we maintain a strong set of firewall, network access control (NAC), remote access, et al. integrations.
Some of our technology partners offer comparable security services to Nozomi Networks in terms of visibility for either assets or network traffic and anomalies, but they do not focus on the specific industrial systems, processes and protocols that are needed for full analysis and actionable intelligence. So, partnering with Nozomi Networks makes great sense to integrate a common, security operations center (SOC)-level view of all IT and OT assets and networks.
Other partners may do data collection and analysis of network environments and traffic, but not from a cybersecurity perspective. They may offer complementary insights or analytics that make sense for industrial systems, while Nozomi Networks provides the cybersecurity visibility they need. With that context, let’s look at some updates to our tech alliances:
Barracuda Networks CloudGen Firewall
As mentioned above, when a Nozomi Networks Guardian device discovers abnormal behavior, it can prevent communications by updating firewall rules and configurations proactively, as needed. This can prevent new, unknown, compromised or malicious devices from attacking the broader network.
Nozomi Networks has recently added the Barracuda Networks CloudGen Firewall to its cadre of firewall partners based on customer demand in our shared markets. Barracuda CloudGen Firewall offers a comprehensive set of next-generation firewall technologies to ensure real-time network protection against a broad range of network threats, vulnerabilities, and exploits, including SQL injections, cross-site scripting, denial of service attacks, trojans, viruses, worms, spyware, and more. The CloudGen lineup includes models for virtually every scale and need from appliances with 1.2 Gbps throughput, all they way up to 52 Gbps.
Two of the primary use cases between Nozomi Networks and Barracuda are node blocking and link blocking. When Guardian generates alerts and incidents, the alert information contains node information involved in the alert. When the node blocking capability is enabled, a node is blocked if it’s unlearned. When Guardian generates alerts and incidents, the alert information may contain link information involved in the alert. When the link blocking capability is enabled, a link is blocked if it’s unlearned, and the nodes connected by the node are not already blocked.

IBM QRadar Now Integrated Into Vantage
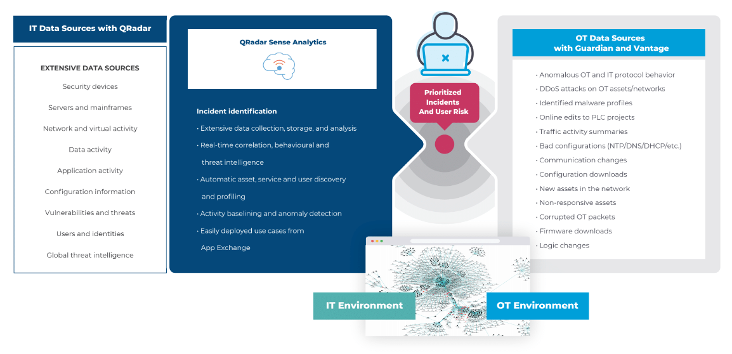
The convergence of IT and OT has created a unique challenge for security teams—protecting large and diverse networks comprised of connected IT, OT, IoT and cyber-physical systems, while maintaining a robust enterprise-wide security posture. That, plus increases in targeted malware campaigns have made network-wide OT/IoT visibility an imperative.
The key is to create a consolidated view into both IT and OT environments. Nozomi Networks and IBM Security have done just that—by integrating Guardian OT and IoT visibility and monitoring with the IBM QRadar security information and event management (SIEM) capabilities. In a single platform, the Nozomi Networks/QRadar solution delivers real-time visibility into the state of the entire OT/IoT environment and identifies potentially malicious activity happening within it.
And now QRadar is integrated into our Vantage cloud-hosted platform, in addition to working with Guardian. The Nozomi Networks QRadar App, which integrates QRadar with Nozomi Networks platforms, is available in the IBM X-Force App Exchange. It is a free extension for the IBM QRadar Security Intelligence Platform. The app delivers out-of-the-box rules and algorithms that plug directly into the QRadar advanced analytics engine. This fully integrated solution provides real-time visibility and threat detection for OT networks, as well as alert aggregation and prioritization for coordinated IT/OT threat management.
ServiceNow Integration for Better Asset Management and Incident Response
Maintaining Configuration Management Database (CMDB) records is a huge overhead for many organizations. Many records are maintained manually, which is an error-prone process and records can quickly become outdated. Nozomi Networks, on the other hand, continuously monitors the network, keeping an always-up-to-date list of assets and their key attributes. When integrated with the Now Platform, live asset data is streamed into the CMDB. This keeps existing records up to date and automatically creates new asset records as needed.
The Now Platform also includes a vulnerability response tracking module. This separate add-on for ServiceNow allows customers to manage remediation efforts of vulnerabilities (for example, triage, assignment, patching, and closure).
Like asset management, vulnerability response is only as good as the data it receives. ServiceNow can scan the network for assets, but OT vulnerabilities are largely a black hole, or more difficult to identify than usual IT devices. We identify assets in OT networks and tell ServiceNow about the known vulnerabilities for this wide range of devices, so the user can remediate them on the ServiceNow side.
The same is true for alerts. Nozomi Networks can provide threat remediation data via our Service Graph Connector (SGC) app. Directly sending threat events to ServiceNow eliminates the errors and tedious processes natural to manual handoffs across systems, teams and responsibilities. Together, Nozomi Networks and ServiceNow can expedite investigation, response, and remediation across IT, Security, and Risk teams to minimize incident impact, data loss, and exposure.










