CVE-2021-26726
A remote code execution vulnerability affecting a Valmet DNA service listening on TCP port 1517 allows an attacker to execute commands with SYSTEM privileges
An un-authenticated network user can craft specific packets targeting a Valmet DNA service, listening by default on TCP port 1517. By exploiting a predictable encryption key, the attacker can trigger commands that will be executed on the remote machine with the SYSTEM privileges.
February 16, 2022
The vulnerability affects the following Valmet DNA versions: Valmet DNA versions from Collection 2012 to Collection 2021
CVE-2021-26726
CVSS:3.1/AV:A/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:P/RL:U/RC:C/CR:H/IR:H/AR:H/MAV:A/MAC:L/MPR:N/MUI:N/MS:U/MC:H/MI:H/MA:H
8.8
The fix is available from Valmet Automation Customer Service
Valmet suggest to use a properly configured firewall to prevent unauthorized access from untrusted networks to the system.
Ivan Speziale of Nozomi Networks
Curated and maintained by Nozomi Networks Labs, the Threat Intelligence™ service provides threat and vulnerability updates to Guardian, making it easy for IT/OT professionals to stay on top of current OT and IoT risks.
Learn more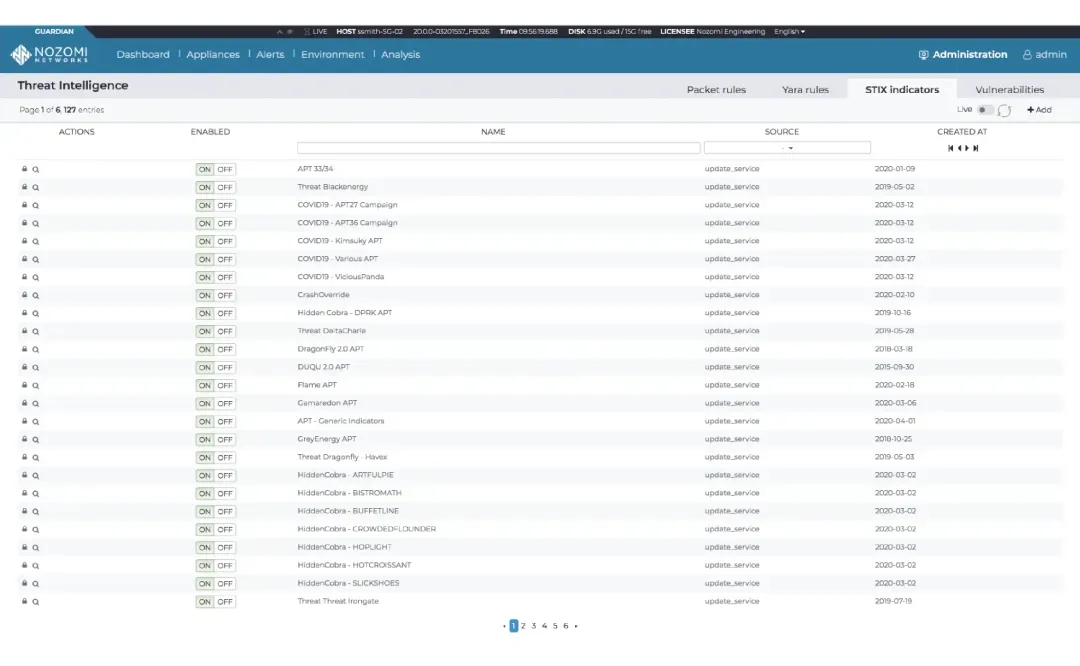

“Threat actors love finding new ways to attack critical infrastructure. We love finding new ways to detect their malware before damage occurs.”
TRITON is the first known cyberattack that directly interacted with a Safety Instrumented System (SIS). Labs reverse engineered the TriStation suite of software and delivered a report and two free tools for security researchers. This research was presented at Black Hat USA 2018.
The Labs team reverse engineered the GreyEnergy malicious document (maldoc) that leads to the installation of the malware (backdoor) on a victim’s network. Project outcomes include a report, multiple blogs and two free tools for security researchers.
IEC Working Group 15 (WG15) is developing technology standards for secure-by-design power systems. Labs contributes to the standards and has demonstrated how they can be used to identify hard-to-detect cyberattacks. Research from this effort was presented at Black Hat USA 2019.