A Note to our Customers and Partners in the Middle East
More InformationCVE-2021-44467
A broken access control vulnerability in the KillDupUsr_func function of spx_restservice allows an attacker to arbitrarily terminate active sessions of other users, causing a Denial-of-Service (DoS) condition, if an input parameter is correctly guessed.
An un-authenticated remote attacker would be able to arbitrarily terminate active sessions to the device of any other user, making it inaccessible.
October 21, 2022
The vulnerability affects: Lanner Inc IAC-AST2500A standard firmware version 1.10.0
CVE-2021-44467
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:L
5.3
Updated BMC firmware versions that fix the issue are available from Lanner technical support
Andrea Palanca of Nozomi Networks
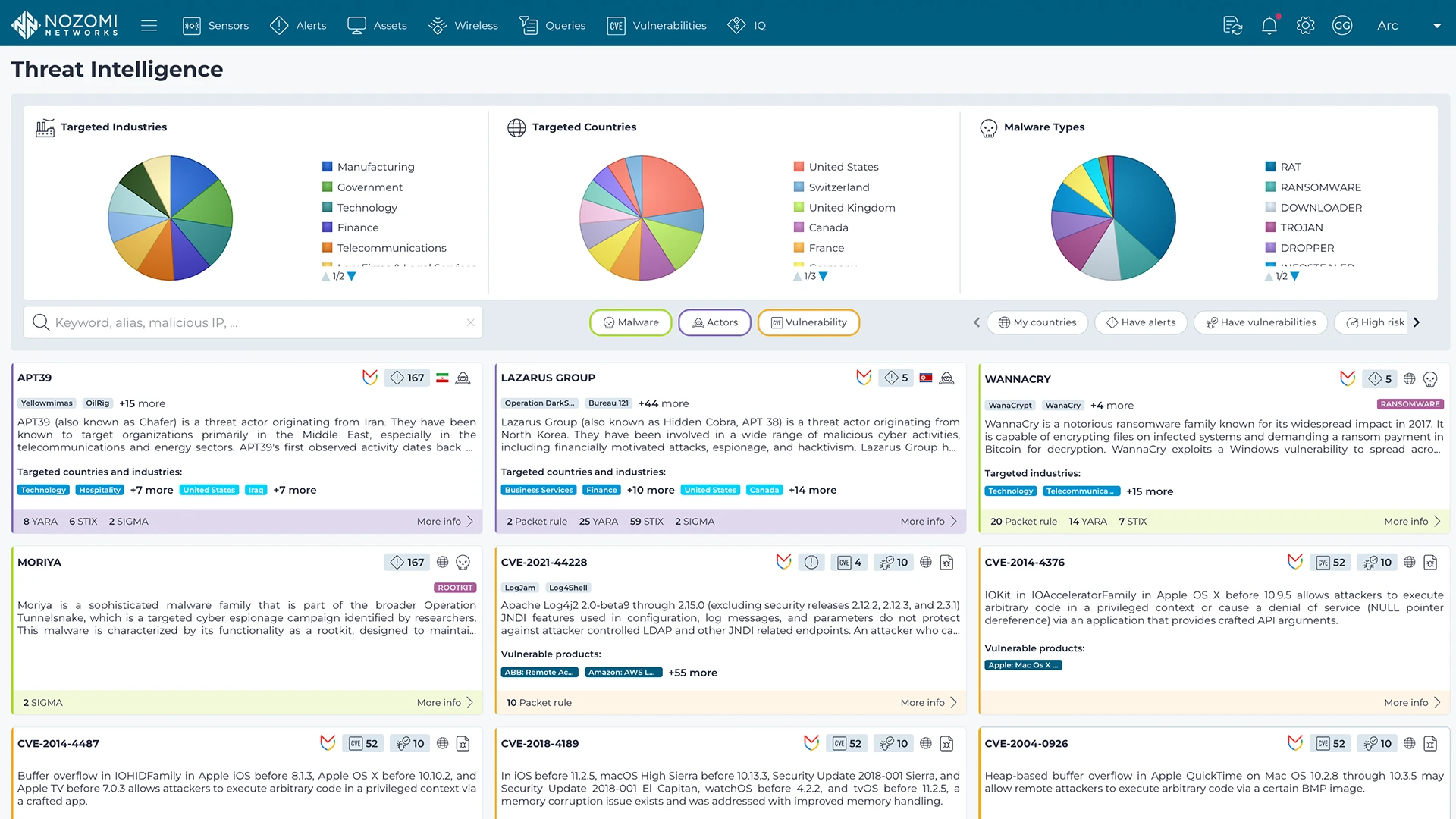
Nozomi Networks Labs curates threat and vulnerability insights that are continuously fed into the Nozomi Networks platform to ensure our sensors can detect existing and emerging threats and vulnerabilities that threaten customers environments.
Learn more