A Note to our Customers and Partners in the Middle East
More InformationCVE-2024-23914
A "CWE-134 Use of Externally-Controlled Format String" vulnerability affects the MC_Open_Association function located in Merative Merge DICOM Toolkit C/C++ on Windows
When MC_Open_Association function is used to open DICOM Association and gets DICOM Application Context Name with illegal characters, it might result in an unhandled exception. The vulnerability can be exploited by unauthenticated attackers with a privileged position in the network.
April 30, 2024
This issue affects: Merative Merge DICOM Toolkit C/C++ on Windows from v5.6.0 up to v.5.17.0
CVE-2024-23914
CVSS:3.1/AV:A/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H
5.7
Update the Merative Merge DICOM Toolkit C/C++ to the 5.18.0 release
Gabriele Quagliarella of Nozomi Networks
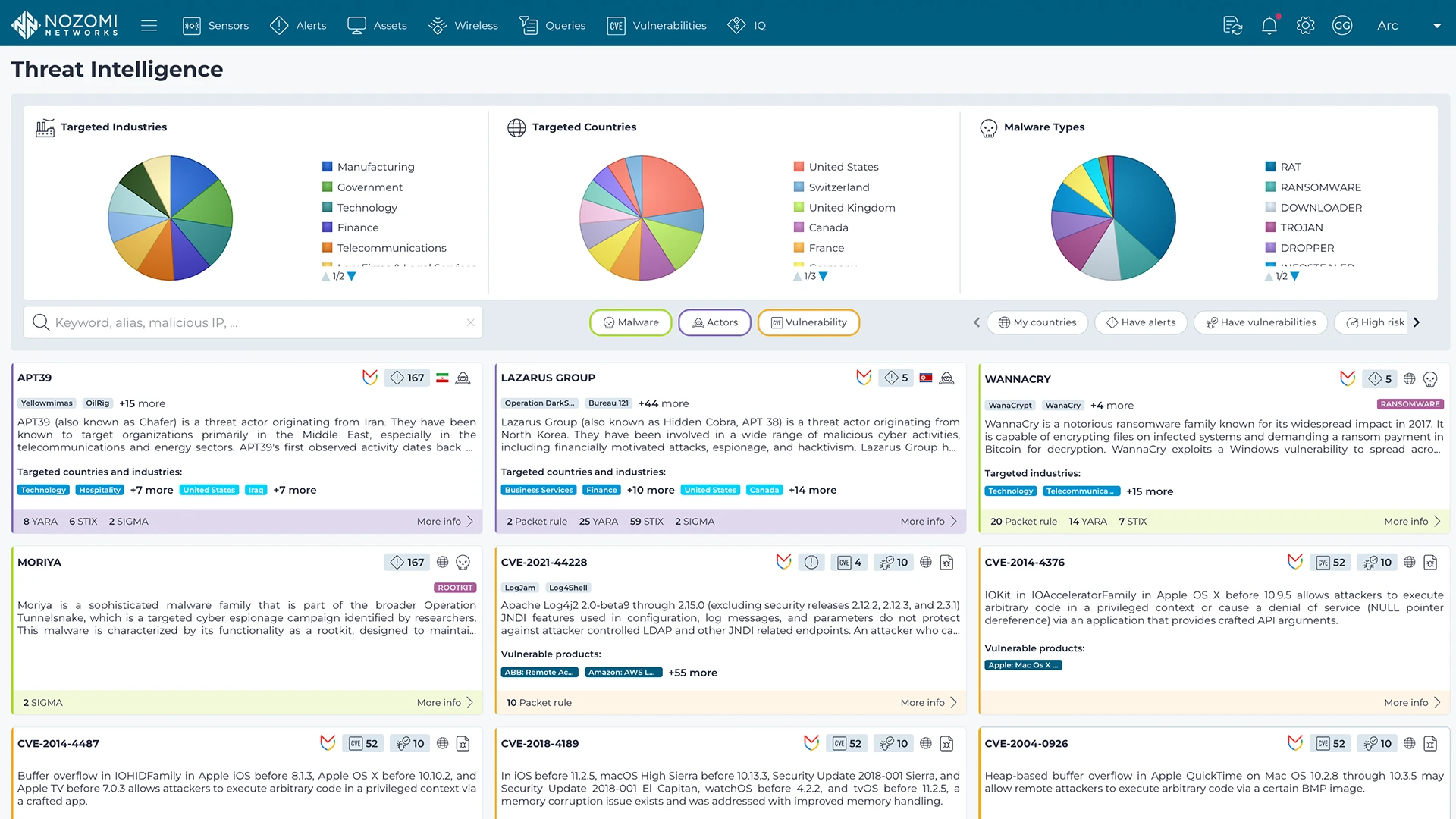
Nozomi Networks Labs curates threat and vulnerability insights that are continuously fed into the Nozomi Networks platform to ensure our sensors can detect existing and emerging threats and vulnerabilities that threaten customers environments.
Learn more