A Note to our Customers and Partners in the Middle East
More InformationCVE-2024-41975
The CODESYS Gateway enables communication between CODESYS runtimes and other clients, primarily the CODESYS Development System V3. It is usually installed as a part of the CODESYS Development System V3 setup and accessed locally by the CODESYS Development System. Due to an insecure standard configuration of the CODESYS Gateway, it is not only accessible locally, but also remotely by default.
The CODESYS Gateway serves as a communication channel for various clients to CODESYS runtimes. By default, the CODESYS Gateway listens on all available network adapters on port 1217 and can therefore be accessed remotely. However, remote access to the CODESYS Gateway is only required in certain network configurations. Since the CODESYS Gateway is usually accessed locally, many users are unaware of this remote access option, which can enable scanning of and access to restricted PLC networks. Unauthenticated attackers can therefore search for PLCs, but the user management of the PLCs prevents the actual access to the PLCs – unless it is disabled.
March 23, 2025
The following products are affected in all versions before 3.5.21.0. • CODESYS Edge Gateway for Windows • CODESYS Gateway for Windows
CVE-2024-41975
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:N/A:N
5.3
Update the following products to version 3.5.21.0. • CODESYS Edge Gateway for Windows • CODESYS Gateway for Windows
Diego Giubertoni of Nozomi Networks
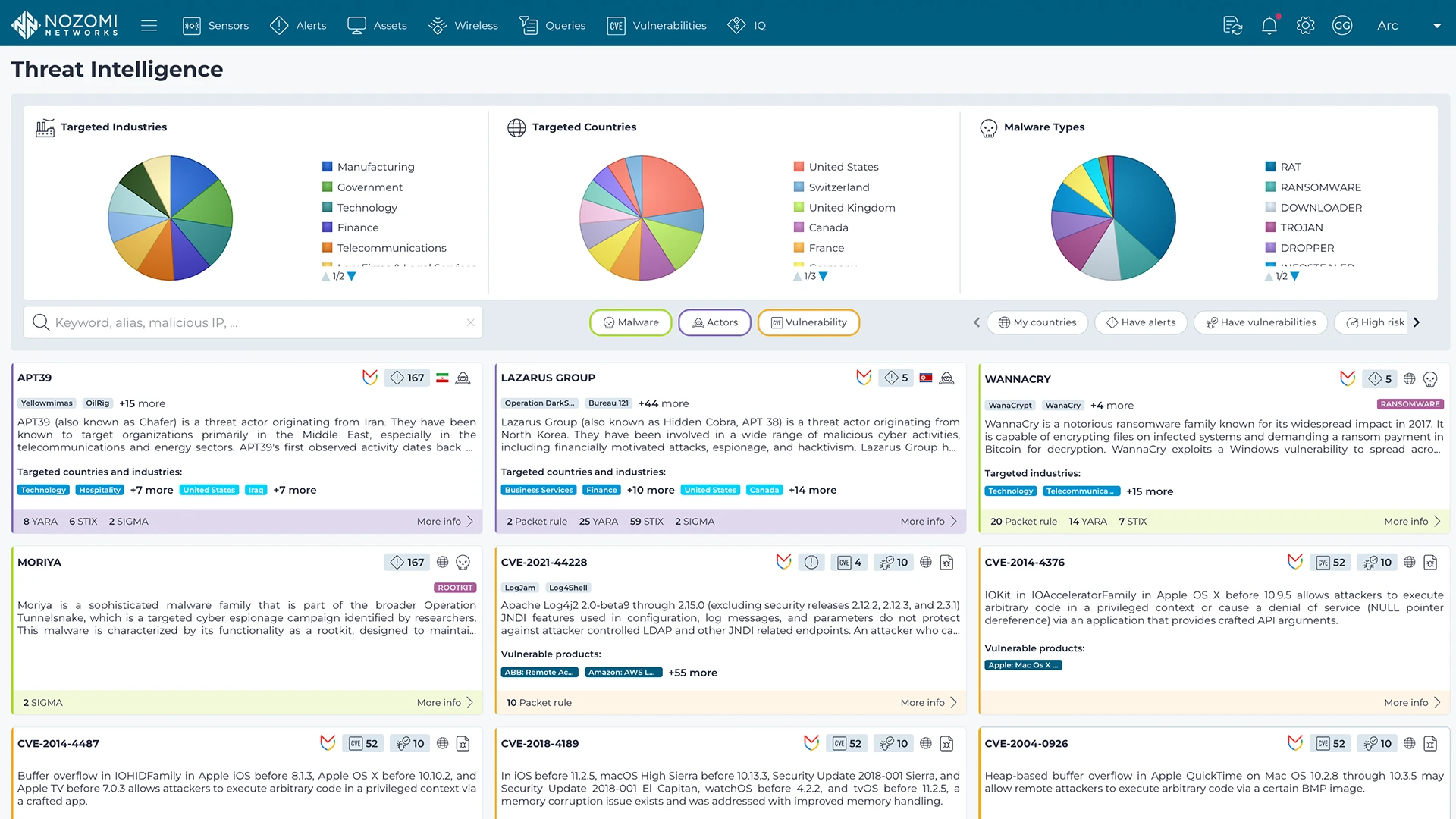
Nozomi Networks Labs curates threat and vulnerability insights that are continuously fed into the Nozomi Networks platform to ensure our sensors can detect existing and emerging threats and vulnerabilities that threaten customers environments.
Learn more