Benefits of the Nozomi Networks Platform
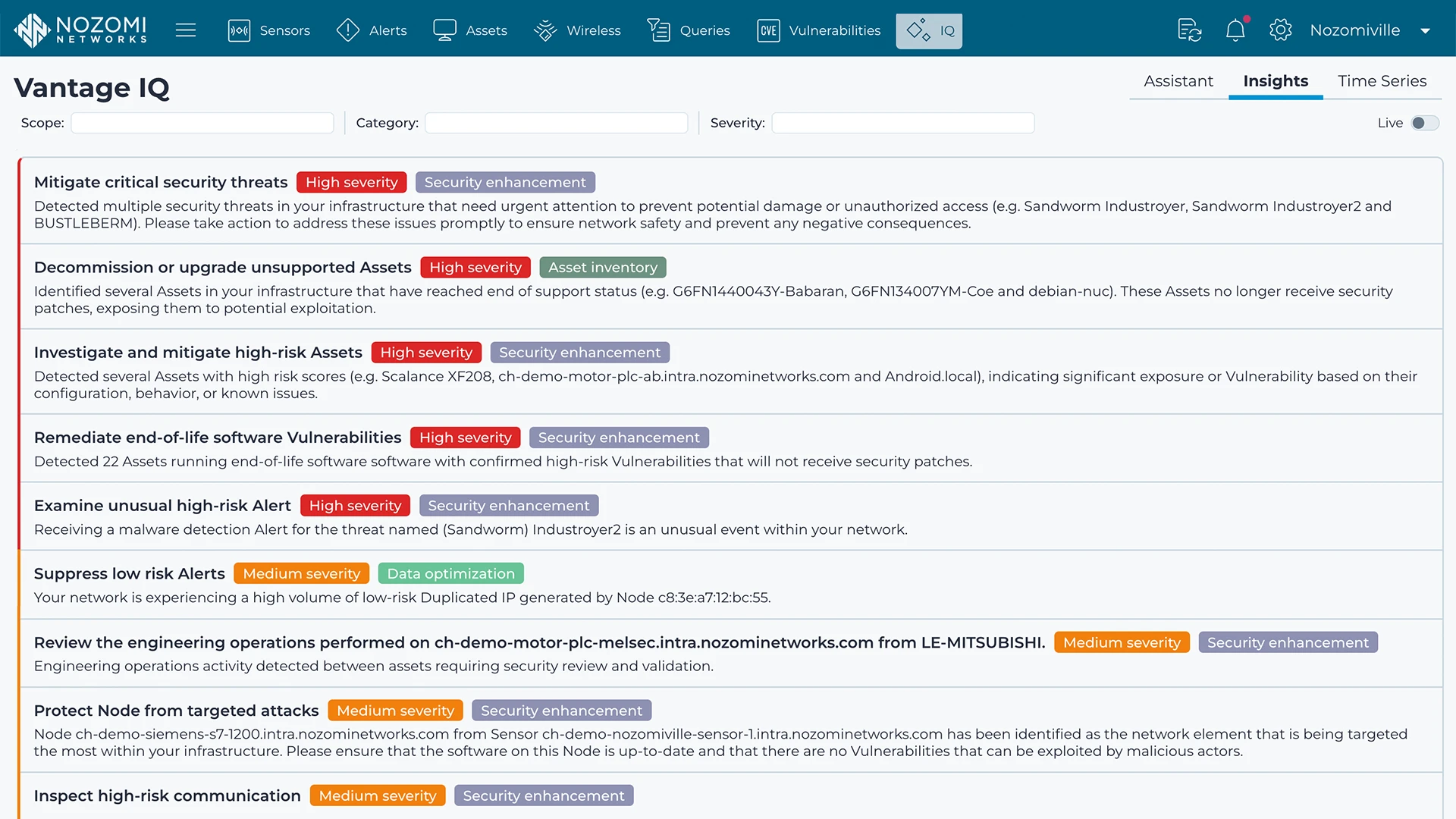
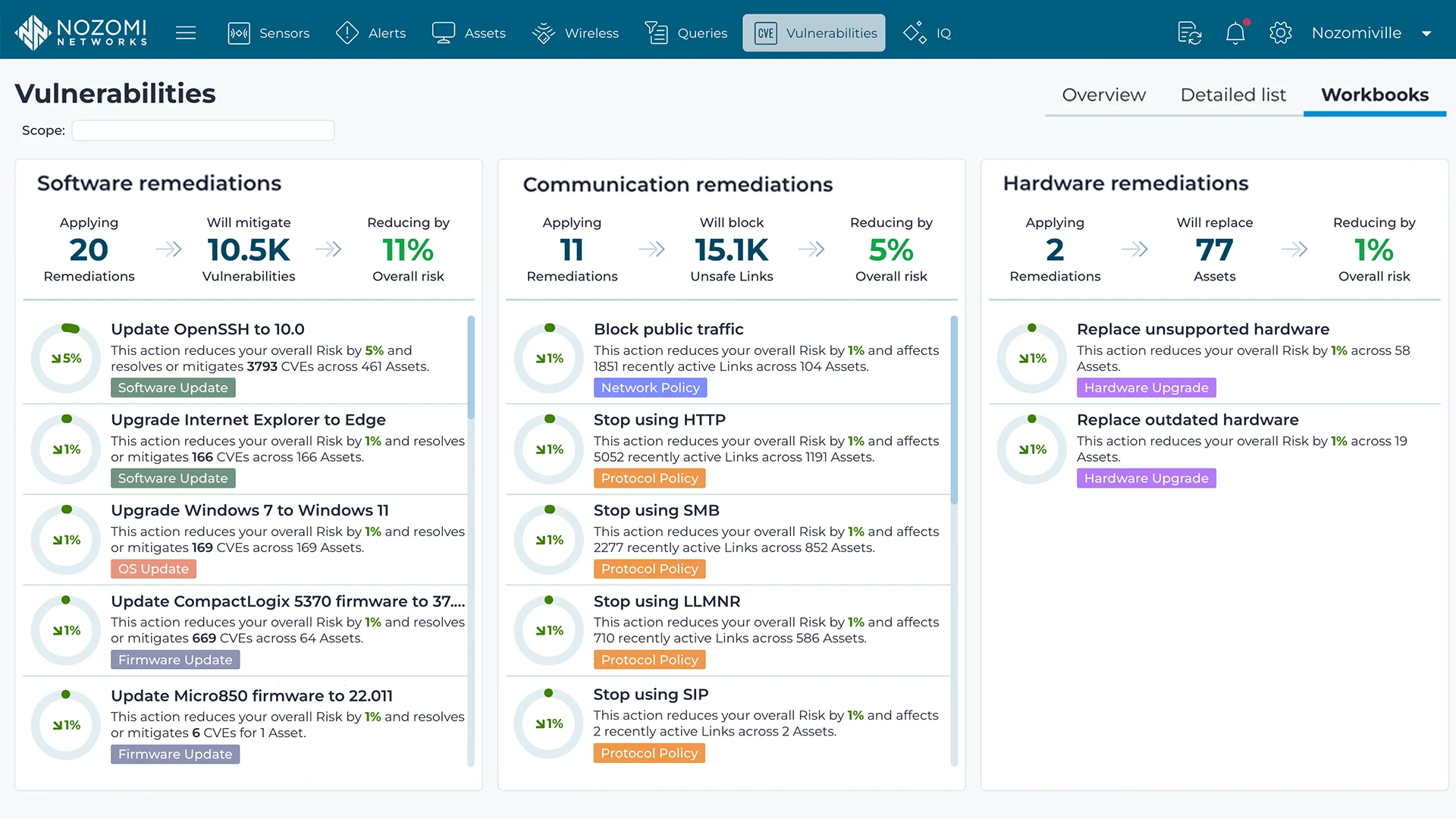
Mitigate Emerging Threats and Vulnerabilities Faster with 100% OT & IoT asset visibility and AI-powered analytics
See how
Benefits of the Nozomi Networks Platform
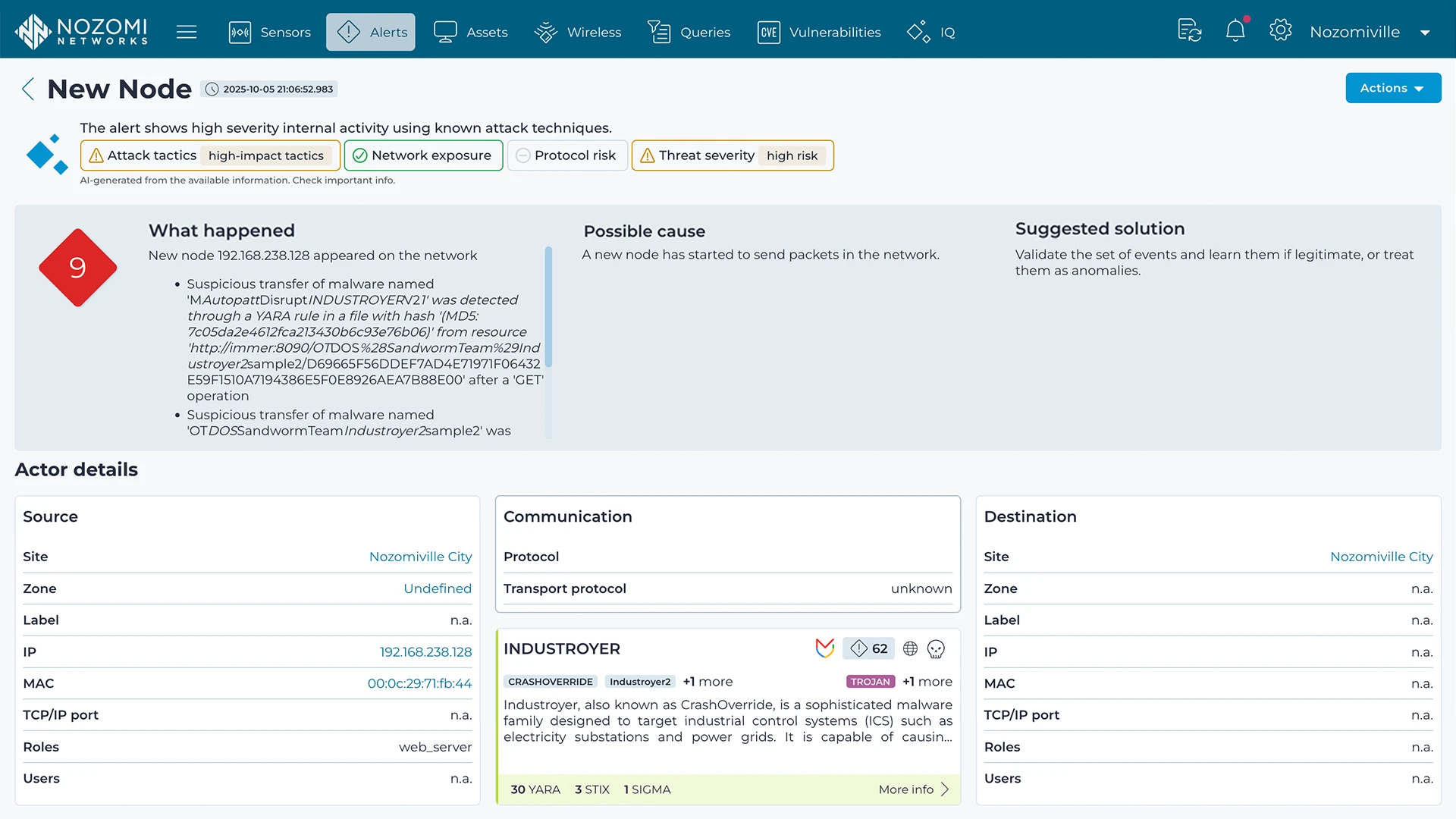
Support Enterprise Risk Management by eliminating OT & IoT security blind spots and enabling integrated analysis and response
See how
Benefits of the Nozomi Networks Platform
Comply with the Toughest Standards & Regulations with releases & reports that keep current with global, regional & industry-specific requirements
See how
Benefits of the Nozomi Networks Platform
Maximize Operational Resilience & Safety with the visibility and security platform your OT engineers trust.
See how


Benefits of the Nozomi Networks Platform
Mitigate Emerging Threats and Vulnerabilities Faster with 100% OT & IoT asset visibility and AI-powered analytics
See how
Benefits of the Nozomi Networks Platform
Support Enterprise Risk Management by eliminating OT & IoT security blind spots and enabling integrated analysis and response
See how
Benefits of the Nozomi Networks Platform
Comply with the Toughest Standards & Regulations with releases & reports that keep current with global, regional & industry-specific requirements
See how
Benefits of the Nozomi Networks Platform
Maximize Operational Resilience & Safety with the visibility and security platform your OT engineers trust.
See how
Benefits of the Nozomi Networks Platform
Mitigate Emerging Threats and Vulnerabilities Faster with 100% OT & IoT asset visibility and AI-powered analytics
See how
Benefits of the Nozomi Networks Platform
Support Enterprise Risk Management by eliminating OT & IoT security blind spots and enabling integrated analysis and response
See how
Benefits of the Nozomi Networks Platform
Comply with the Toughest Standards & Regulations with releases & reports that keep current with global, regional & industry-specific requirements
See how
Benefits of the Nozomi Networks Platform