A Note to our Customers and Partners in the Middle East
More InformationThe Nozomi Threat Intelligence subscription provides continuous insights into the unique attack techniques and vulnerabilities specific to OT and IoT processes and devices. Detailed threat information in the form of Yara, packet and Sigma rules; STIX and vulnerability indicators; and threat definitions is sent to Guardian network sensors, Arc endpoint sensors and the Vantage cloud management platform, so you can detect and respond more quickly.
The Nozomi Networks Labs team analyzes threat and vulnerability information from more than a dozen public and private data sources, as well as anonymized telemetry from across our customer base.
Continuously updated OT and IoT threat intelligence is tightly woven into the platform to enrich asset and network data and enable better detection of anomalies, malicious behavior and threats.
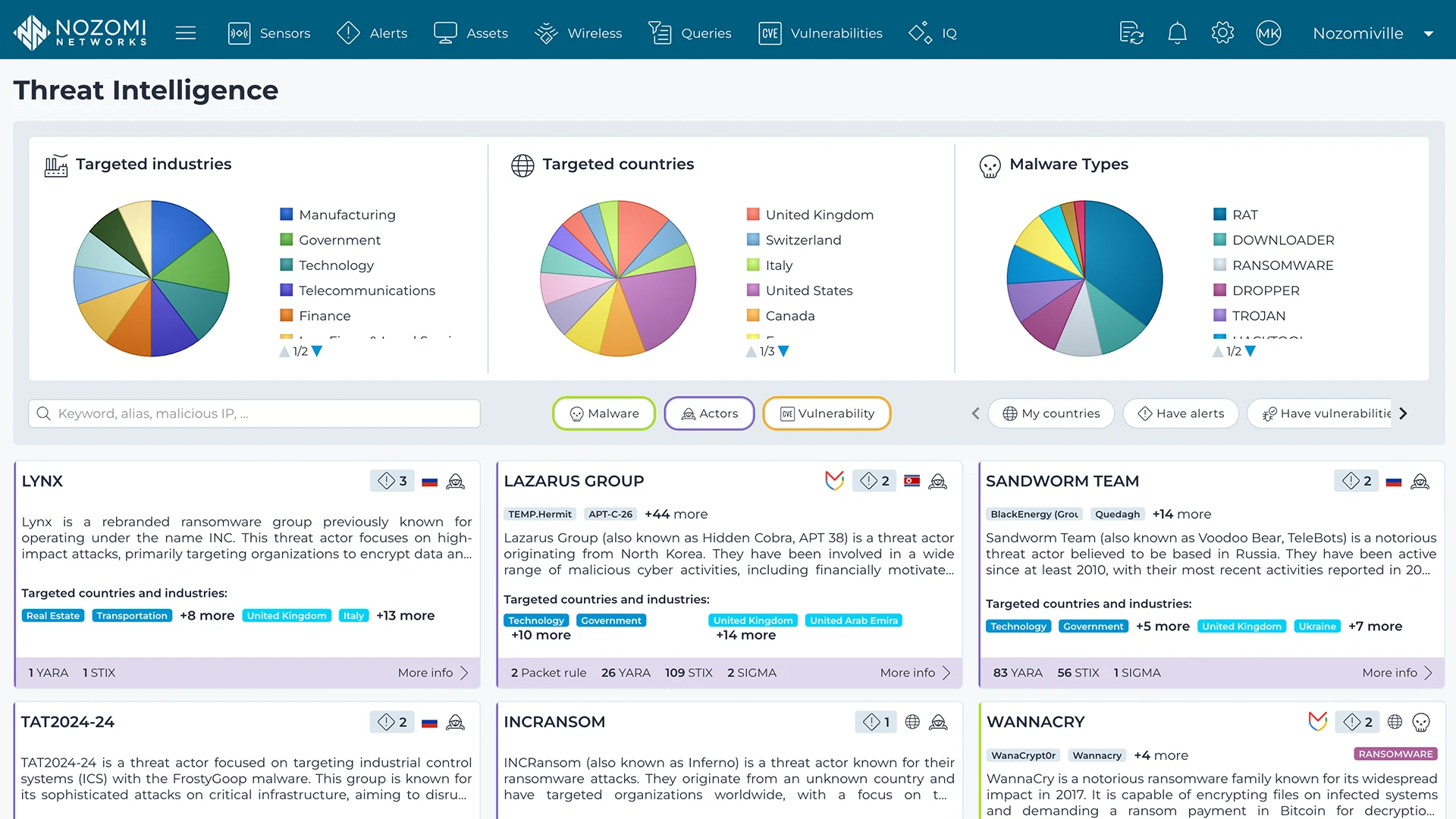
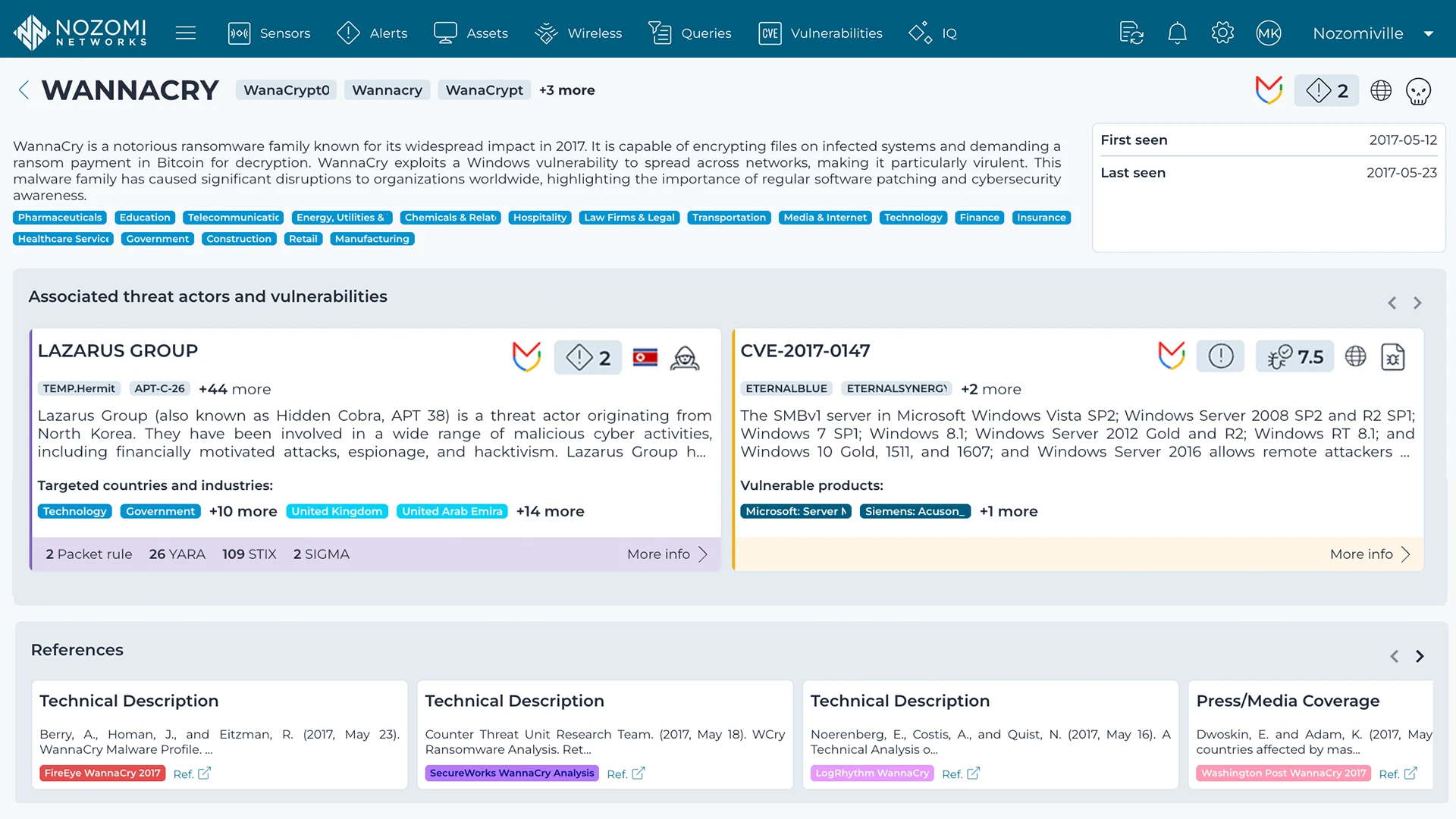
Threat intelligence is distilled into information-packed threat cards available in Vantage, with details on threat actors and associated exploits, malware, vulnerabilities and MITRE ATT&CK® TTPs, with mitigation suggestions and links to external references.
Distinct from Mandiant’s core IT-centric threat intelligence, the Nozomi TI Expansion Pack, Powered by Mandiant integrates relevant Mandiant IOCs and TTPs into our intelligence feed and threat cards, including IT-borne threats that can move into OT.