Reports of an OT‑focused malware allegedly targeting water treatment facilities, ZionSiphon, have been receiving significant attention online. After a detailed technical review of the malware sample, Nozomi Networks Labs' analysis indicates that it is unlikely to be a genuine, operational threat. Instead, multiple inconsistencies in functionality, incomplete execution paths, and a limited understanding of how industrial plants work strongly suggest it is a mock-up or non-functional proof of concept, possibly created to simulate malicious behavior rather than carry out real-world attacks.
While the ZionSiphon sample has been widely discussed and amplified, our findings challenge the narrative that this represents an active or emerging threat in the wild.
In this post, we share our assessment of these claims and outline what is most relevant for organisations operating in OT environments. As the malware sample has already been analyzed, we focus instead on key aspects of those findings that warrant further consideration from an OT security perspective, drawing broader conclusions about how such malware would behave and interact in a real-world environment if it were operational.
Technical Analysis: Inconsistencies That Undermine Credibility
Based on our analysis of ZionSiphon, several features appear unrealistic and inconsistent with real-world water treatment operations. While individual functions are relatively clear in intent, a broader review of the sample reveals gaps that raise questions about how the components fit together.
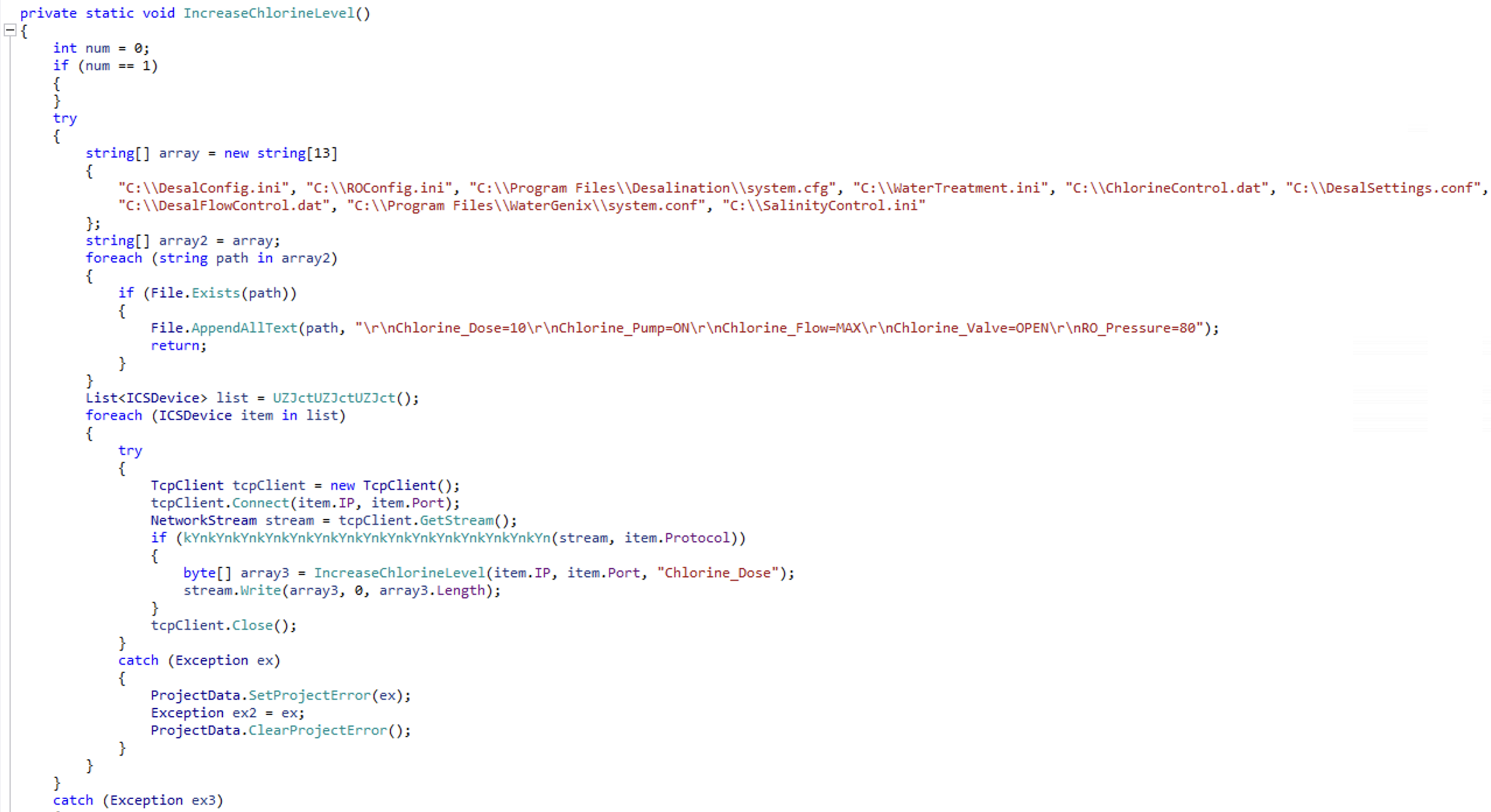
Fabricated Configuration Paths: Signs of LLM-Generated Code
There are no real-world references to the hardcoded configuration filenames as they seem to be fabricated and resembling the kind of generic output an LLM might produce when asked to suggest configuration paths for a water desalination plant (e.g., C:\DesalConfig.ini, C:\WaterTreatment.ini, C:\ChlorineControl.dat). The formats of the configuration filenames vary greatly (some are .ini, others .dat or .cfg or .conf), yet the function responsible for modifying them handles all of them in the exact same way by appending the following line-separated key-value pairs:
- Chlorine_Dose=10
- Chlorine_Pump=ON
- Chlorine_Flow=MAX
- Chlorine_Valve=OPEN
- RO_Pressure=80
Flawed Geofencing Logic
The sample includes a function to ensure that it only executes in Israel, which is the target country. The function tries to determine the host’s geolocation by retrieving the network interface's local IP address and then checking it against hardcoded IP ranges associated with the target country. Malware typically relies on external services to determine the host’s public IP address, as this method would not work in NATed environments.
Information Hiding Inconsistencies
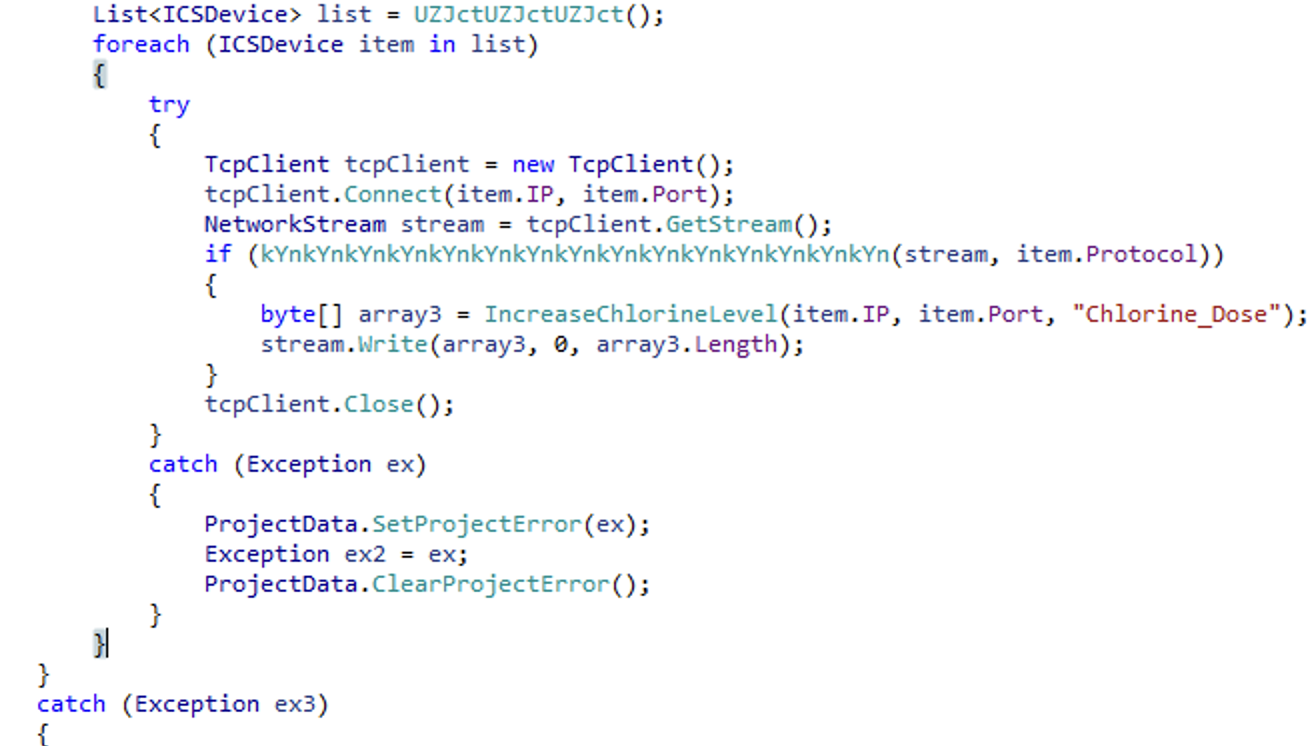
Many strings in the sample are base64-encoded, presumably to evade basic detection mechanisms. However, other, more sensitive strings remain in plaintext (e.g., “IncreaseChlorineLevels”, “IsDamDesalinationPlant”, “IsTargetCountry”), which undermines any consistent attempt at obfuscation.
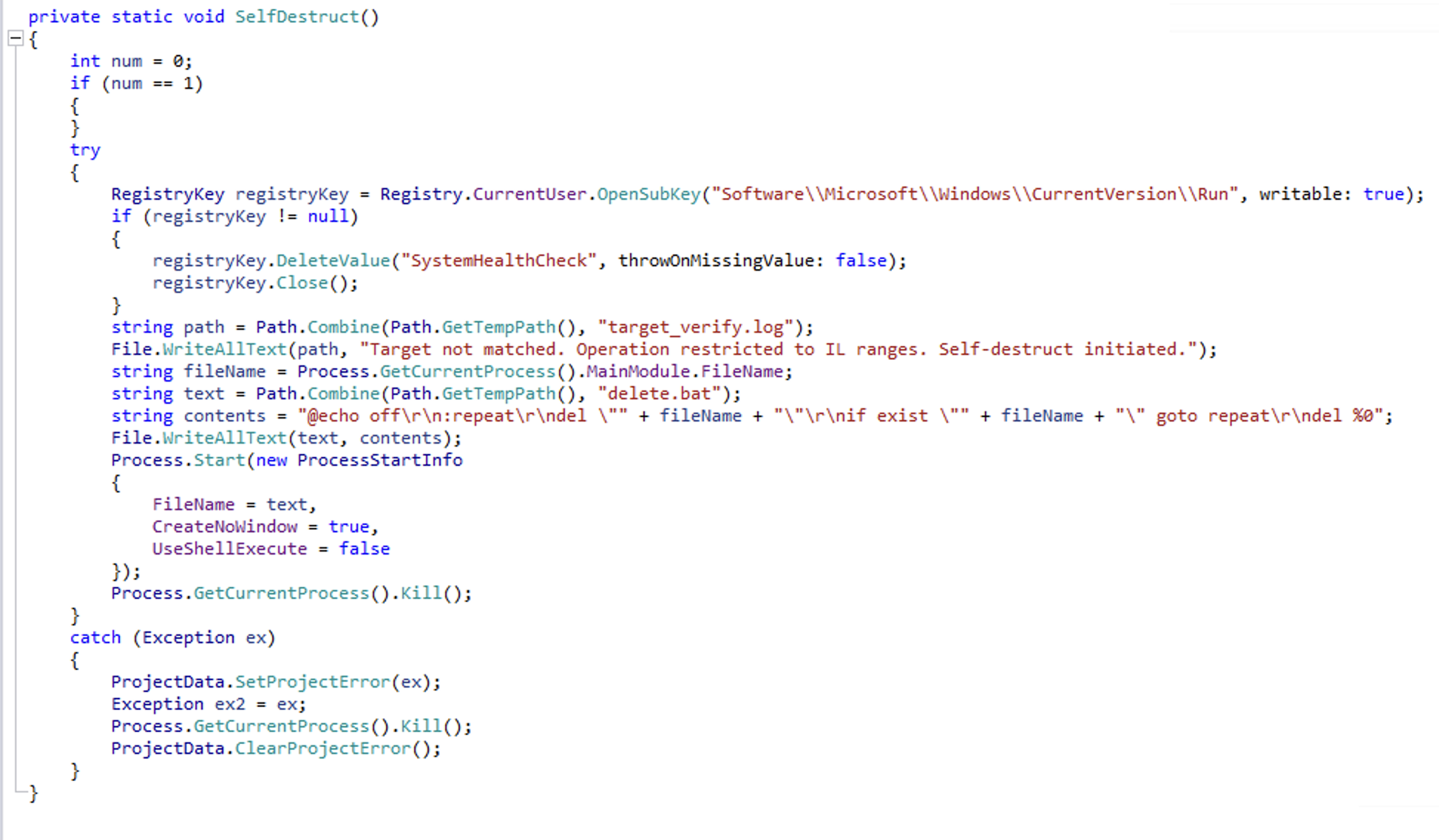
The sample also includes a self-destruct mechanism intended to restrict execution to targeted environments. However, this function writes the message “Target not matched. Operation restricted to IL ranges. Self-destruct initiated.” to a file named “target_verify.log,” a behaviour that contradicts any realistic requirement for stealth.
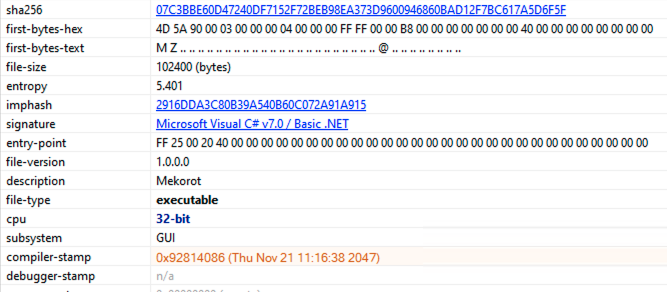
Suspicious Compiler Timestamp
A compiler timestamp date set in the future is more likely to raise suspicion than to provide any real benefit. While malware authors often manipulate timestamps to obscure the true compilation date, using one that is clearly unrealistic is a crude approach that needlessly draws attention.
OT Protocol Interaction
Previously observed OT malware typically includes configurations that tailor its operation to the specific target environment. For example, Industroyer2 embeds network-specific parameters such as IP addresses, ports, and IEC-104 details, including Information Object Addresses, while the original Industroyer relies on an external .ini file to customize its behavior. Achieving physical impact requires precise mappings between protocol values and the underlying physical processes, which vary across vendors and installations.
In contrast, the analyzed sample attempts to modify parameters such as “chlorine level” and “turbine speed” dynamically by querying Modbus registers at runtime and inferring their meaning based solely on numeric ranges.
Would ZionSiphon Work in a Real Water Treatment Plant?
In addition to the malware's multiple technical faults, its operational logic does not align with the reality of how water and desalination plants operate. It’s not as simple as setting a MAX value on a Chlorine control point via a config file or Modbus command.
Real control systems don't typically read process setpoints from flat files at runtime. For the Modbus writes to be effective, the malware would need to know the exact register addresses for chlorine dose and pressure setpoints at the specific target facility. Modbus has no directory service. There is no "chlorine setpoint register" that is standardized across vendors. The author would need facility-specific documentation or prior reconnaissance to write to the correct registers.
Even with all this in place, there are still physical limitations on the system as well as the safety engineering and safety systems. On the physical side, pumps are sized for the normal operating range. Chemical metering pumps are designed with sufficient capacity to dose at peak flow conditions while maintaining sufficient turn-down to avoid overdosing during low-flow periods. They are not oversized, as this adds cost and complexity. A pump designed to deliver 2 ppm into a 10 Mgal/d flow cannot suddenly deliver 1000 ppm. The physics of pump stroke, speed, and chemical tank volume won't allow it.
On the safety side, there are water-quality monitoring systems, PLC logic, hardware interlocks, and most importantly, human operators who monitor these plants to keep our water safe. Good physical engineering should make even a working cyber attack of this type not impactful. Alongside operators, cyber defenders work to keep our water supply safe. While water cybersecurity is underfunded, some facilities have good security in place, and it's safe to assume that some referenced sites in the malware are on that list, given past attacks and current geopolitical realities.
Conclusion: ZionSiphon Is Demonstrative Code, Not a Deployable Threat
Our analysis of the ZionSiphon sample finds no evidence of a credible capability to operate against real-world OT environments. While the code is structured to resemble industrial malware, its implementation lacks the coherence, domain awareness, and precision required to achieve meaningful physical impact. The inconsistencies, incomplete logic, and unrealistic assumptions highlighted throughout this analysis point to a constructed or experimental artifact rather than a functional threat.
This does not diminish the importance of continued vigilance in the OT security space. Sophisticated malware targeting industrial systems has demonstrated the level of planning and environment-specific knowledge required to succeed. In contrast, ZionSiphon illustrates how superficial indicators of malicious intent can be mistaken for operational capability when examined without sufficient technical context.
The widespread attention given to this sample underscores the need for careful validation and technical rigor when assessing potential threats. Distinguishing between demonstrative code and genuinely deployable tooling is critical to maintaining an accurate understanding of the threat landscape and avoiding unnecessary alarm.
Mitigation and Recommendations
While ZionSiphon does not represent a credible operational threat, it is a reminder that the OT threat landscape continues to evolve — and that accurate, timely threat intelligence matters.
Nozomi Networks Labs has updated our Threat Intelligence package to detect this ZionSiphon sample beginning with version 2026/03/18 [202603180507_26feafd]. No customer action is required at this time beyond maintaining normal monitoring and update practices.
While we assess with high confidence that this malware does not pose a direct risk to our customers, we recognise the value of providing visibility into emerging OT threats. To support this, we have updated our detection metadata to reflect the latest naming, making it easier to identify related activity.
Nozomi Networks provides industrial and critical infrastructure organizations with deep visibility into OT and IoT environments, enabling teams to detect anomalous behavior, monitor for emerging threats, and respond with confidence. The Nozomi Networks Labs team continuously analyzes new malware samples, publishes threat intelligence, and updates detection capabilities to keep customers ahead of real and emerging risks.
To learn how Nozomi can help protect your industrial operations, contact our team or request a demo.