“Without rapid containment, Sandworm does not disengage. It accelerates.”
Recent geopolitical events involving publicly disclosed attacks against national critical infrastructure across Europe and the U.S., have once again drawn attention to a highly disruptive threat actor known as Sandworm, the Russian state-sponsored group also tracked as APT44, Seashell Blizzard, and Voodoo Bear. By studying environments where Sandworm activity has been positively identified, we can extract lessons that help future victims detect intrusions earlier, recover more effectively, and — most importantly — prevent Sandworm-related incidents altogether.
To better understand this notorious threat actor’s operational patterns and real-world impact, Nozomi Networks conducted a deep analysis of its observed behaviors, the systems it affects and the damage it leaves behind. To do so, we examined anonymized telemetry from 10 industrial customers in seven countries spanning July 2025 through January 2026. Within this corpus, 29 events were conclusively identified as Sandworm activity.
Here’s what we learned.
Key Findings from Analyzing Sandworm Activity
Nozomi collects and analyzes a vast array of threat intelligence drawn from multiple sources, including direct customer and partner engagements, curated third-party intelligence feeds, honeypot research, anonymized customer telemetry and insights from our internal threat research team. These findings leverage all of these sources.
- Activity aligns with Moscow office hours and a bureaucratic execution model, with execution peaking midweek after lunch.
- Lateral movement is a core feature of Sandworm operations, with infected machines generating thousands of lateral alerts.
- Old, highly damaging malware remains in active use, allowing Sandworm to capitalize on already compromised environments rather than attempt novel exploits.
- Every infected system generated weeks, or months, of serious advance warnings — on average for 43 days.
- Rather than retreating when detected, Sandworm escalates — raising severity, expanding tooling and shifting focus toward ICS and OT to impact operations.
What Is Sandworm?
Sandworm is a Russian state-sponsored cyber threat group attributed to GRU Unit 74455, Russia’s military intelligence cyber sabotage unit. The group is widely recognized for conducting some of the most destructive cyber operations ever observed, including the Ukrainian power grid attacks and the 2017 NotPetya outbreak.
Sandworm’s operations overwhelmingly target government entities and critical infrastructure, blending espionage, attack and influence operations in direct support of Russian military and geopolitical objectives. Its actions typically have taken place leading up to offensive, kinetic military operations such as in Ukraine.
In addition to the GRU, other Russian cyber units operate on behalf of the FSB (internal counterintelligence agency and successor to the Soviet-era KGB) and the SVR (civilian foreign intelligence agency). These actors all focus on long-term espionage. Financially motivated ransomware groups are also often tolerated by the Russian state.
Sandworm stands apart for its willingness to cause immediate, visible damage.
Key Differences Between Sandworm and Other Threats
1. Mission and Intent
Ransomware groups are primarily financially motivated. Hacktivists are typically influenced or publicity driven and rarely pursue sustained operational damage.
Unlike either of these groups, Sandworm operates as a state-directed military cyber-sabotage unit, with a mission focused on disruption and physical world impact rather than profit or long-term espionage.
2. Target Selection
Ransomware operators usually prioritize IT environments where payment leverage is highest. Hacktivists tend to focus on public-facing systems, websites or symbolic targets rather than industrial control systems (ICS).
Sandworm deliberately targets government entities and critical infrastructure, including ICS and OT environments.
3. Willingness to Cause Physical Disruption
Sandworm has a documented history of pursuing operations intended to cause real-world harm, such as power grid disruption and destructive wiper activity.
Most other threat actors, even when destructive, stop short of actions that risk physical damage or safety impacts.
4. Operational Behavior
Sandworm activity aligns with Russian government working hours and follows a structured, bureaucratic execution model, indicating centralized tasking and oversight.
Criminal and hacktivist activity is generally more opportunistic, irregular and less tightly coordinated.
5. Post Detection Response
Many ransomware actors reduce activity or exit an environment once discovered. In some cases they’ve dissolved their gang and regrouped or rebranded.
Sandworm escalates when detected, expanding activity, increasing severity and shifting focus toward ICS and OT assets rather than disengaging.
6. Use of Existing Compromises
Sandworm frequently leverages environments that are already compromised, capitalizing on non-remediated exploit chains and longstanding security gaps rather than relying on novel zero-day exploits.
This contrasts with the perception that highly capable actors primarily leverage new or exotic tooling.
Bottom line: Sandworm stands apart because it combines state sponsorship, deliberate ICS targeting and a demonstrated willingness to cause physical and operational disruption. This places it in a fundamentally different risk category than state-sponsored espionage, ransomware groups or hacktivists and explains why its activity is often treated as a strategic warning indicator rather than a conventional cybercrime problem.
Recent Events Tied to Sandworm
For historical context, here are selected events tied to this threat actor, many of them notorious:
Dataset Overview
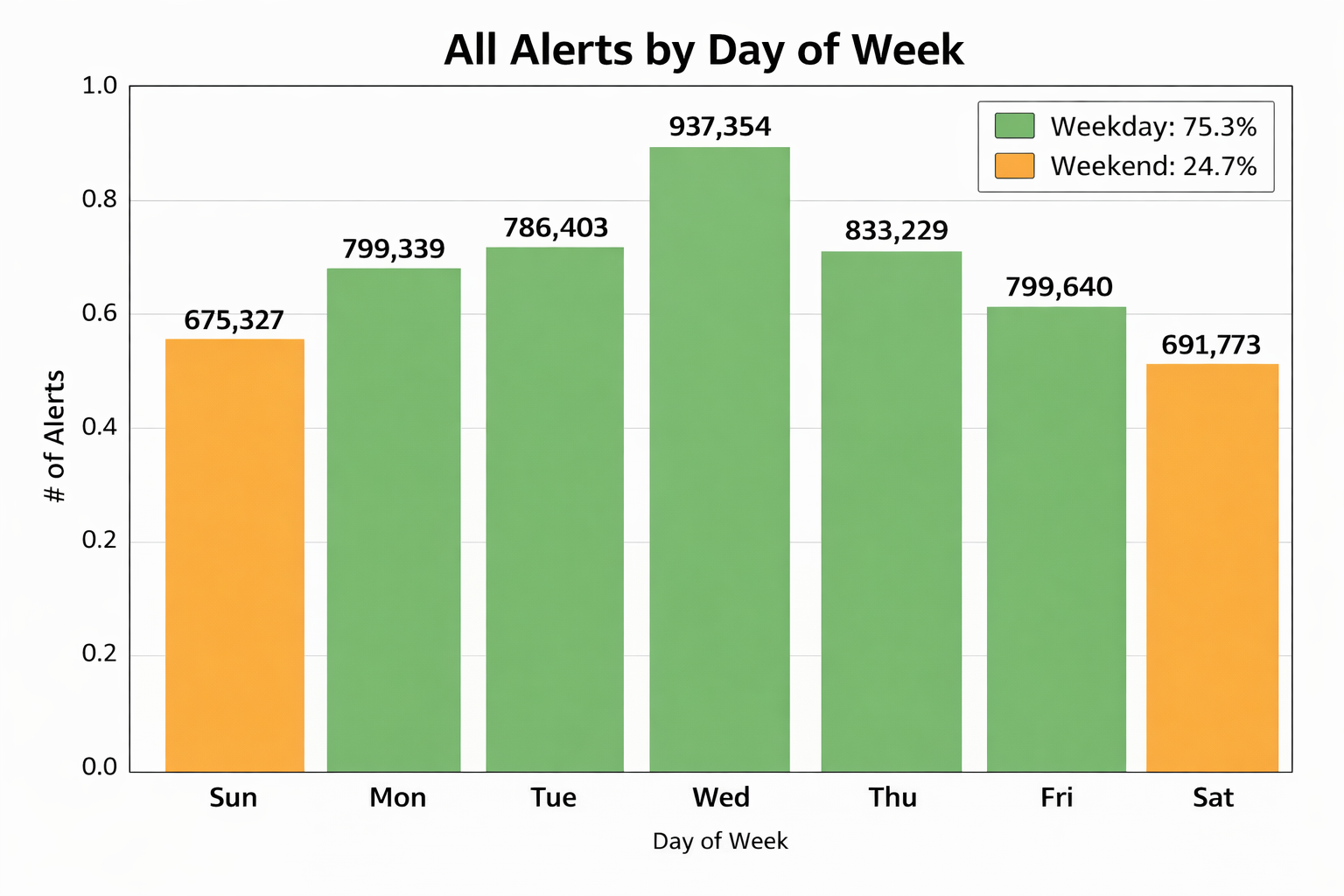
Our analysis examined a focused subset of anonymized telemetry consisting of 5,543,865 alerts collected from 10 industrial customers across seven countries — the U.S, Mexico, U.K., Germany, Belgium, Colombia and Thailand — spanning July 2025 through January 2026.
These organizations operate in the manufacturing and transportation sectors, including pharmaceuticals, food production, motor vehicles, computer equipment and textiles. This data directly correlates to what is detailed in our 2025 2H OT/IoT threat report. The anonymized telemetry contains detailed network metadata including source and destination IPs, ports, protocols, threat classifications and (where applicable) MITRE ATT&CK® for ICS mappings, including ICS asset types and Purdue Model levels.
Of the total alert volume, 1,141,348 alerts (20.6%) originated from ICS classified source assets, spanning engineering workstations, field controllers (RTUs, PLCs, IEDs), and human machine interfaces (HMIs). Within this corpus, 29 events were conclusively identified as Sandworm activity using signature-based detections, including YARA rules and validated threat intelligence indicators. Within the dataset we sliced, the earliest detection we observed occurred on August 13, 2025, with the last on January 14, 2026. However, it’s important to note that detections have happened before and after the dataset we’re focused on for this exercise.
Key Findings: Diving Deeper into Sandworm
1. Activity Aligns with Moscow Office Hours and a Bureaucratic Execution Model
Sandworm activity strongly correlates with standard Russian government working hours, peaking midweek and during post-lunch business hours, with Wednesday at approximately 2:00 PM Moscow time showing the highest alert volume.
This timing suggests the activity is not opportunistic or ad hoc, but rather executed as part of a structured, task-driven workday. In Russian government and military bureaucracies, operational rhythms commonly follow a predictable pattern:
- Monday: tasking stabilization
- Tuesday: coordination, clarification and approvals
- Wednesday: execution begins in earnest
- Thursday – Friday: reporting, cleanup and preparation
The observed alignment reinforces the conclusion that Sandworm operations are centrally directed and professionally executed, rather than the result of after‑hours or freelance activity.
LOTL (Living off the Land) depends on human operators using legitimate tools and access, rather than automated malware. Mapping LOTL activity to a clock or calendar helps distinguish likely actors from automated systems.
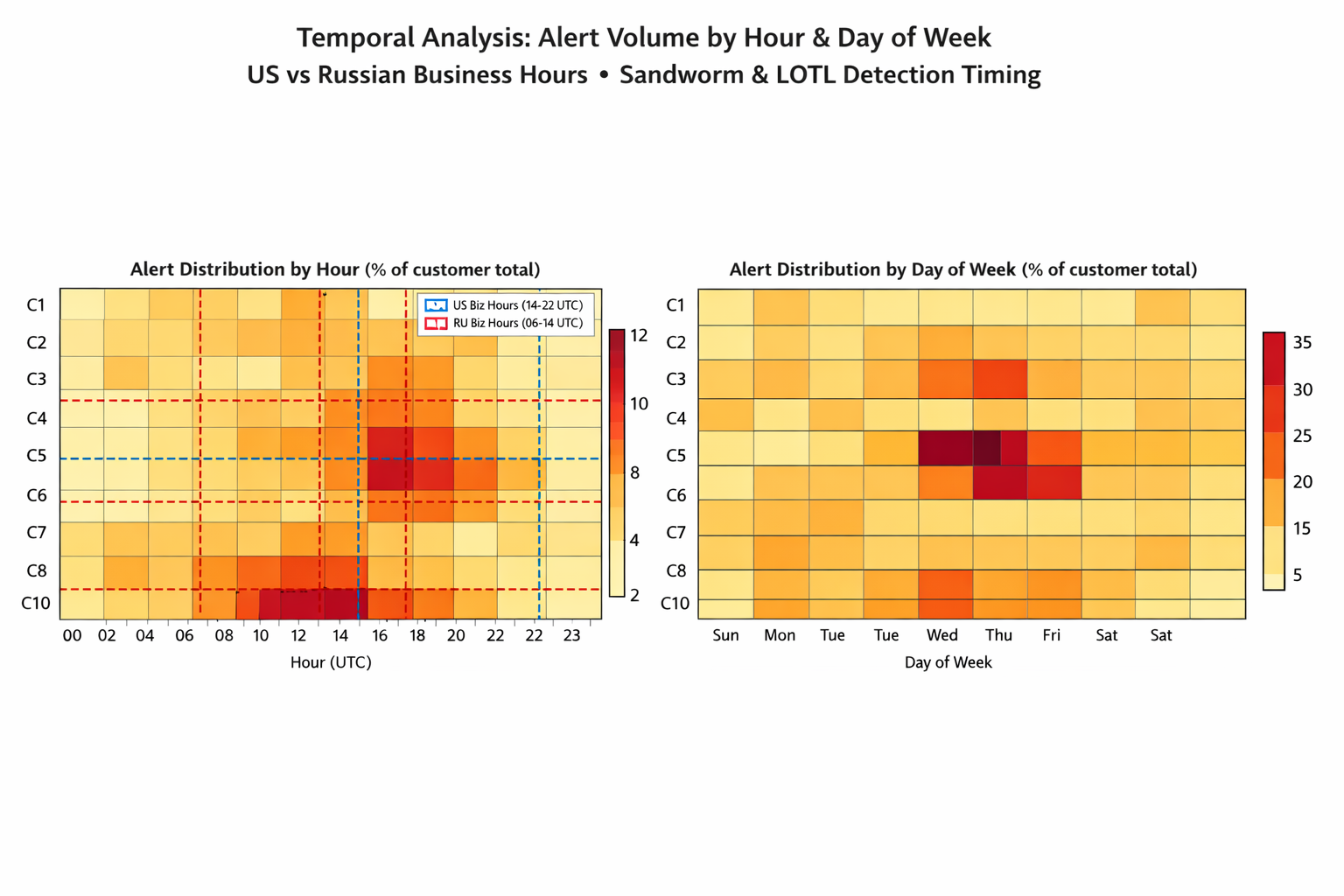

We do not have visibility into, or direct data from, the attack on the Polish power grid. However, when we align the timeline of that incident with our broader activity analysis, the periods overlap precisely with when Sandworm would have been operationally focused on executing that attack chain.
During this same window, we observed a measurable slowdown in their activity elsewhere. Specifically, the rate at which they acquired new victims decreased by approximately 2.2x. From early November 2025 through January 2026, Sandworm averaged one new victim every 24.7 days, compared to their prior pace of one new victim every 11.4 days before the grid attack.
This suggests a temporary reallocation of resources and operational focus toward the Polish grid operation, at the expense of broader targeting activity.
2. Lateral Movement Is a Core Feature of Sandworm Operations
Across the dataset, 17 Sandworm-infected machines were identified across the 10 customers. Following initial detection, these systems conducted lateral movement against 923 unique internal targets.
Notably:
- 632 target machines began generating entirely new alert types after being contacted.
- In the most extreme case, a single infected system attempted lateral movement against 405 internal targets.
- One infection event triggered a 12-fold increase in alert volume.
This aggressive lateral movement highlights Sandworm’s focus on rapid internal expansion once footholds are established.
3. Old, Highly Damaging Malware Remains in Active Use
Despite widespread awareness and patch availability, Sandworm continues to rely on older but proven exploit chains, including EternalBlue, DoublePulsar and WannaCry.
In fact, the pattern was consistent: systems compromised by Sandworm were already heavily infected before Sandworm activity began. Specifically:
- Three victims that experienced the widest lateral movement already showed active EternalBlue → DoublePulsar → WannaCry exploit chains.
- Four more victims had ongoing command and control activity using commercial frameworks such as Cobalt Strike, Metasploit and other Remote Access Trojans (RATs).
- A second wave of infections at three victims leveraged Log4Shell as the initial access vector.
Sandworm did not need novel exploits; it simply capitalized on environments that were already compromised.
4. Every Infected System Generated Weeks — or Months — of Advance Warnings
Perhaps the most critical finding: every single Sandworm infected system produced 20 to 155 days of warning alerts prior to Sandworm activity.
- Average duration of serious warnings: 43 days
- Alerts included well-known exploit chains and active C2 communications
In practical terms, investigating any of these alerts — EternalBlue, Cobalt Strike, RAT activity or Log4Shell exploitation — would likely have revealed compromised systems well before Sandworm arrived. At minimum, remediation efforts would have hardened the environment enough to prevent Sandworm from using these systems as launch points.
These were not stealthy zero-day attacks. These were noisy, well-documented techniques that went uninvestigated. Sandworm effectively moved into environments that were already “owned.”

5. Sandworm Escalates When Detected
In every affected environment, Sandworm activity intensified after detection in at least one dimension. An important consideration in this finding is that it’s unknown if Sandworm threat actors knew that they were detected. Rather than retreating, the actor escalated…raising severity, expanding tooling, and shifting focus toward ICS and OT to impact operations.
ICS assets were directly targeted, including 286 Engineering Workstations at one victim, 102 in another, and 13 in a third victim. Also, industrial control systems such as Field Controllers, RTUs, PLCs, IEDs were directly targeted in 3 victims, resulting in 52 targets in 1 victim, and the others having a handful each. In another victim, 95 HMIs were targeted.
The targeting of Level 1 and 2 Purdue assets from infected machines confirms OT-specific intent.
Escalation Dimensions
1. Alert Volume
Daily alert rate increased after Sandworm detection (normalized for observation window length).
2. Alert Type Variety
More distinct alert categories fired post-detection, indicating a broader attack surface.
3. Threat Diversity
More unique malware and threat identifiers observed, implying new tools were deployed.
4. New Attack Types
Brand-new alert types that never appeared before detection, revealing novel TTPs.
5. Target Expansion
More unique destination IPs contacted, indicating wider lateral movement across the victim network.
6. Port Expansion
More destination ports probed, suggesting deeper service enumeration and reconnaissance activity.
7. MITRE Danger Shift
ATT&CK tactic gravity shifted toward Impact and Inhibit Response, indicating more dangerous intent.
Dimensional Escalation Summary
Across victims, there was a multi-dimensional escalation pattern, not just a single spike:
- 2 victims experienced escalation across 6 dimensions
- 1 victim experienced escalation across 5 dimensions
- 4 victims experienced escalation across 4 dimensions
- 2 victims experienced escalation across 3 dimensions
- 1 victim experienced escalation across 2 dimensions
Most victims did not just see more alerts. They experienced broad behavioral escalation across multiple dimensions simultaneously, with the majority showing increases in 4–6 out of 7 dimensions.
This indicates coordinated post-detection adaptation rather than random noise or isolated changes.



Without rapid containment, Sandworm does not disengage. It accelerates.
In sum, Sandworm is an advanced persistent threat that warrants close monitoring, as its cyber activity has historically preceded real‑world military or geopolitical actions. This threat differs from ransomware groups or hacktivists in that it deliberately targets industrial control systems and conducts operations intended to cause physical and operational disruption.
Recommendations for Defending Against Sandworm
1. Treat “commodity” alerts as strategic warnings, not noise
Why it matters:
Every Sandworm-infected system in the dataset generated weeks to months of high-confidence warnings — including EternalBlue, Cobalt Strike, RAT activity, and Log4Shell exploitation — before Sandworm activity occurred.
Recommendation:
- Prioritize investigation and remediation of well-known exploit chains and active C2 alerts, even if they appear routine or historically tolerated.
- Assume unresolved commodity compromises can become state actor launch points, not just ransomware precursors.
Defensive takeaway:
If you can reliably eradicate EternalBlue, Log4Shell, and post-exploitation frameworks, you significantly reduce Sandworm’s ability to establish or expand footholds.
2. Harden environments before Sandworm arrives
Why it matters:
Sandworm consistently leveraged pre-compromised environments, rather than relying on zero-day exploits.
Recommendation:
- Focus on baseline hygiene: asset risk-based vulnerability management, credential hygiene, removal of exposed admin services and elimination of legacy protocols.
- Validate that previously identified compromises are fully remediated, not just contained.
Defensive takeaway:
Sandworm does not need advanced access if defenders leave doors open. Preventing initial compromise is more effective than reacting to Sandworm-specific indicators.
3. Monitor and constrain lateral movement aggressively
Why it matters:
Sandworm infections demonstrated extreme lateral movement, with single hosts targeting hundreds of internal systems and causing massive alert amplification.
Recommendation:
- Detect and respond rapidly to abnormal internal scanning, authentication attempts, and service enumeration.
- Enforce network segmentation between IT and OT, and within OT zones where possible.
- Treat any system performing large-scale lateral movement as a high-severity incident, regardless of malware family.
Defensive takeaway:
Stopping lateral movement early limits Sandworm’s ability to pivot toward ICS assets.
4. Prioritize protection of ICS-adjacent systems
Why it matters:
Sandworm directly targeted Engineering Workstations, HMIs and Field Controllers, confirming deliberate OT intent.
Recommendation:
- Apply heightened monitoring and access controls to engineering workstations and ICS management hosts.
- Ensure these systems are not used for general IT tasks or internet browsing.
- Treat any compromise of ICS-adjacent assets as a potential precursor to physical impact.
Defensive takeaway:
Engineering systems are not just endpoints—they are operational choke points.
5. Do not expect Sandworm to disengage after detection
Why it matters:
Sandworm consistently escalated activity after detection, increasing severity and shifting focus toward OT rather than backing off.
Recommendation:
- Prepare incident response plans that assume post-detection escalation, not attacker withdrawal.
- Move quickly from detection to containment and isolation, especially for systems with OT access.
- Avoid partial remediation that leaves attackers room to adapt.
Defensive takeaway:
Detection without decisive containment increases risk.
6. Align defensive readiness with geopolitical risk
Why it matters:
Sandworm activity historically aligns with Russian military and geopolitical operations and follows predictable bureaucratic execution patterns.
Recommendation:
- Increase vigilance during periods of heightened geopolitical tension involving Russia and critical infrastructure.
- Treat Sandworm detections as strategic warning indicators, not isolated cyber incidents.
- Ensure executive leadership understands the physical and operational risk implications.
Defensive takeaway:
Sandworm activity is often a signal, not just an intrusion.
Bottom Line
Defending against Sandworm is less about exotic detection techniques and more about discipline:
- Investigate early warnings
- Eliminate long‑standing compromises
- Contain lateral movement decisively
- Protect ICS-adjacent assets as mission-critical systems
Organizations that consistently address these fundamentalsdramatically reduce Sandworm’s ability to operate, even without Sandworm-specificintelligence.