A Note to our Customers and Partners in the Middle East
More InformationCVE-2023-6949
A Missing Authentication for Critical Function issue affecting the HTTP service running on the DJI Mavic Mini 3 Pro on the standard port 80 could allow an attacker to enumerate and download videos and pictures saved on the drone internal or external memory without requiring any kind of authentication.
An adjacent attacker may exfiltrate pictures and recorder videos from the drone memory.
March 29, 2024
This issue affects: Mini 3 Pro on all firmwares.
CVE-2023-6949
CVSS:3.1/AV:A/AC:L/PR:L/UI:R/S:U/C:H/I:N/A:N
5.2
DJI didn't recognize the issue as a vulnerability, for this reason no fix has been delivered. The vulnerability is marked as "disputed".
Diego Giubertoni of Nozomi Networks
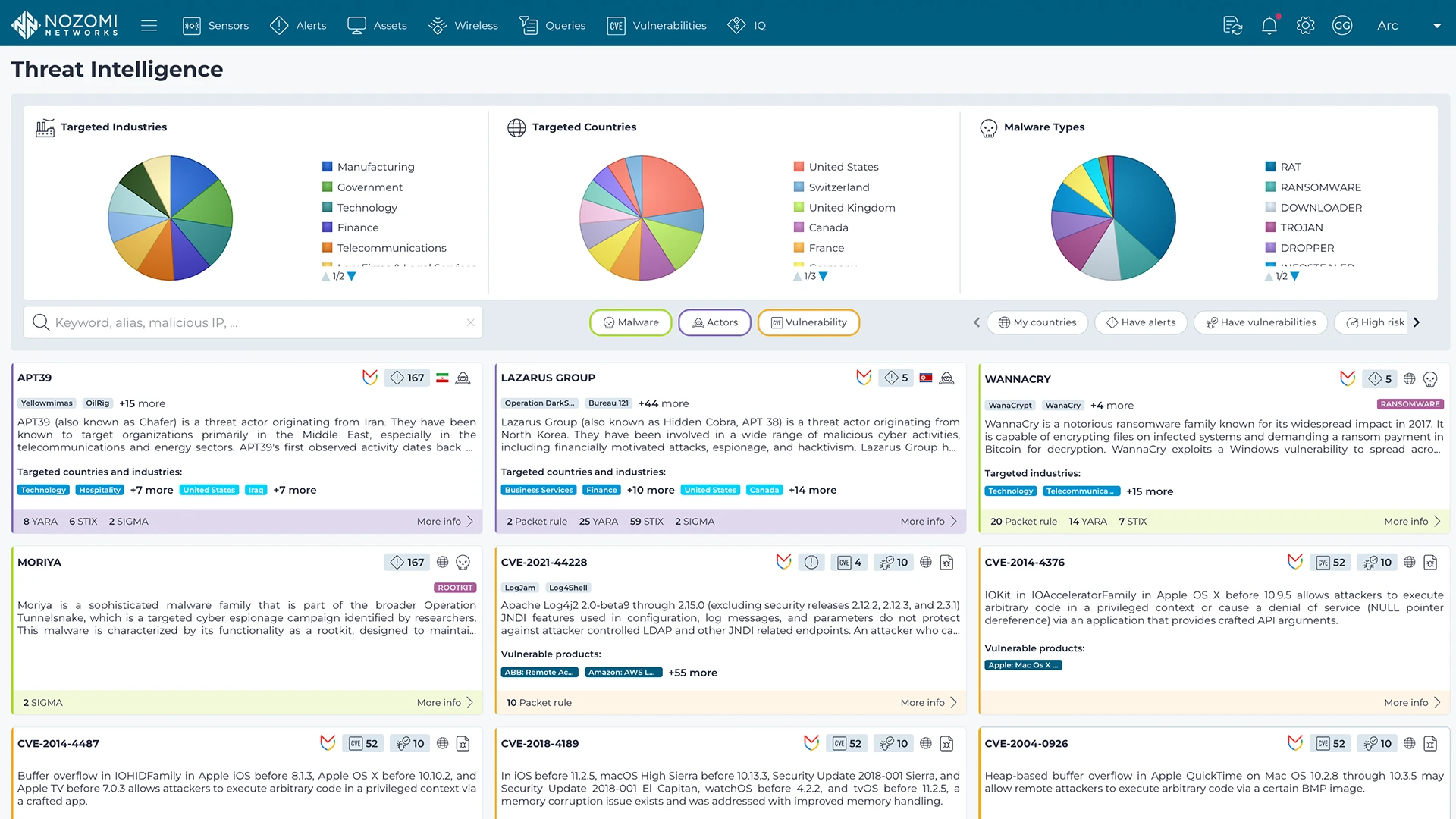
Nozomi Networks Labs curates threat and vulnerability insights that are continuously fed into the Nozomi Networks platform to ensure our sensors can detect existing and emerging threats and vulnerabilities that threaten customers environments.
Learn more