This post is part of a blog series that recaps highlights from our webinar series of the same name in which NERC CIP-015 experts share their knowledge and field lessons from utilities on their internal network security monitoring (INSM) journey.
NERC CIP‑015 is no longer a theoretical exercise. For many utilities, the transition from awareness to implementation is well underway.
In our second webinar in this series, we shared insights based on what we’re seeing across dozens of utilities independent power producers (IPPs) at different stages of their INSM journey. Some organizations are just getting started. Others are already audit‑ready for CIP‑015‑1, but all are not yet prepared for the expanded scope of CIP-015-2.
Let’s break down where things stand today, what’s changing with CIP‑015‑2, and how regulated entities can set themselves up for success.
CIP-015-1 and CIP-015-2 Enforcement Dates to Target
After years in drafting, CIP-015-01 was approved by FERC at the end of June 2025. The implementation timeline provides a phased approach focused on control rooms first. Yet, in speaking with utilities, one of the biggest points of confusion we discuss is around timelines, perhaps because (a) there are so many different entity types subject to different deadlines, and (b) the 015-2 standard revision, which is still pending, introduces additional deadlines.
As with other NERC CIP standards, you must be compliant by the enforcement date. When you strip it down to the essentials, the enforcement dates for 015-1 and 015-2 look like this:
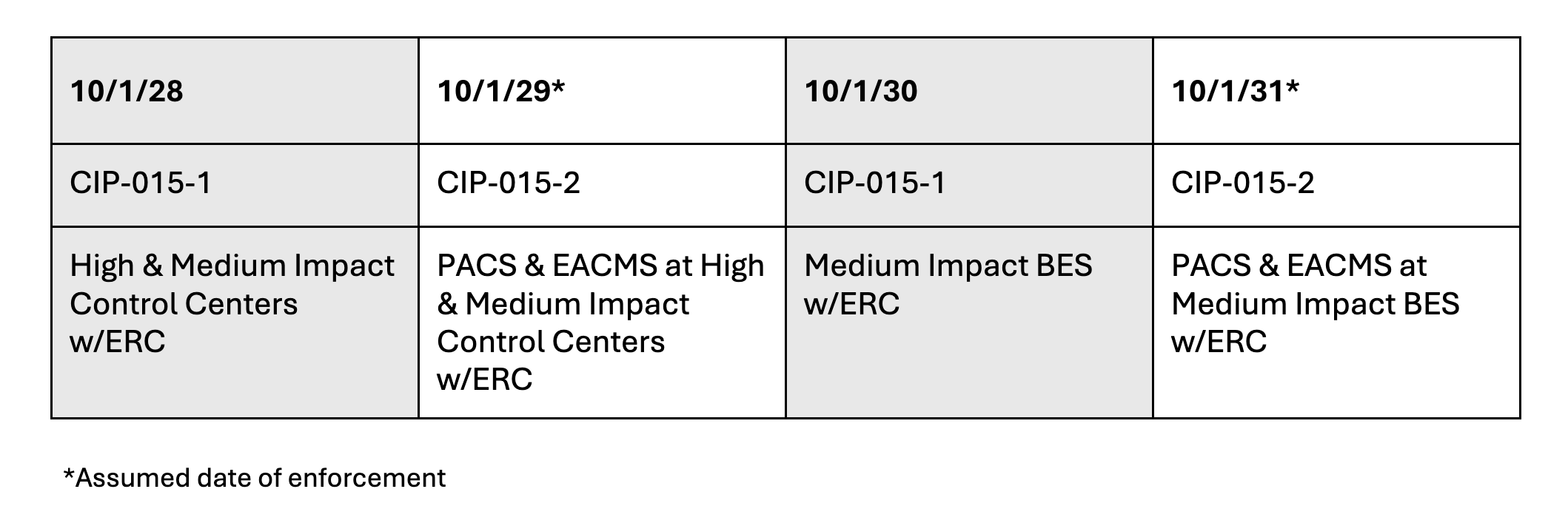
NERC CIP-015-1 Deadlines
Focusing just on 015-1, the deadlines are October 2028 and 2030. The first deadline affects all High and Medium Impact Control Centers with External Routable Communication (ERC). That expands two years later to all Medium Impact BES with ERC, your substations and medium generation facilities. In practice, there aren’t many Medium Impact generation facilities compared to Low Impact ones; however; these facilities will take the longest to roll out INSM, so don’t wait. Low Impact and IBR Category 2 assets are not currently in scope, although industry conversations about future expansion continue.
NERC CIP-015-2 Deadlines
The 2029 and 2030 deadlines for CIP-015-2 are forecasts for now. We won’t have exact dates until FERC approves the revised standard. If there’s one takeaway, it’s this: dates that seem far away have a habit of arriving quickly once you account for design, procurement, deployment and integration work.
CIP‑015‑2 and the “CIP-Networked Environment”
CIP‑015‑2 expands visibility requirements beyond traditional monitoring within the Electric Security Perimeter (ESP), bringing two asset classes squarely into focus:
- EACMS (Electronic Access Control and Monitoring Systems)
- PACS (Physical Access Control Systems)
While both were expected to come into scope, the operational reality is far from simple. One of the main issues is the so-called “CIP-networked environment,” the term you may hear NERC use to describe what’s now included. If it doesn’t sound familiar, that’s because it’s not an official NERC glossary term. That distinction matters.
In practice, the CIP-networked environment includes:
- Assets inside the ESP
- EACMS
- PACS
- Associated communications and traffic flows
What it doesn’t automatically include are unrelated systems that share a network segment — unless traffic or functional dependency brings them into scope. This is where things get tricky.
The larger, more mature programs have segmented off these components, but many utilities and IPPs (especially smaller or less mature programs) have environments that weren’t designed with CIP-015-2 in mind. They typically have shared resources, with multiple things outside the ESP in one DMZ or multiple logical DMZs. A lot of the complexity builds over time due to mergers, acquisitions, new technology deployments and new security directives. Understanding what talks to what, why and over which paths becomes the real work. You end up with devices and traffic all over the place that this standard forces you to make sense of, particularly within your PACS.
PACS: The Core Challenge of CIP‑015‑2
If there’s one area that consistently raises questions when discussing CIP-015-2, it’s PACS. Unlike EACMS, which often follow more predictable architectures, PACS environments can include:
- Card readers, controllers, cameras and badge systems
- Shared systems that secure the Physical Security Perimeters (PSPs) and none-in-scope areas
- Back‑end networks
- IP and non‑IP devices
PACS have a wide range of components and architectures that can make it hard to define what is in scope and how to monitor it:
- Where do we draw the boundary?
- Which devices and traffic are actually in scope?
- Do cameras count, and if so, which ones?
There’s no shortcut here. A deep architectural review is essential. For some entities replacing or upgrading the PACS may be easier and more cost effective than trying to add INSM monitoring to a legacy system.
Where Are Most Utilities Today with INSM?
From what we’re seeing across the industry, utilities generally fall into one of five stages:
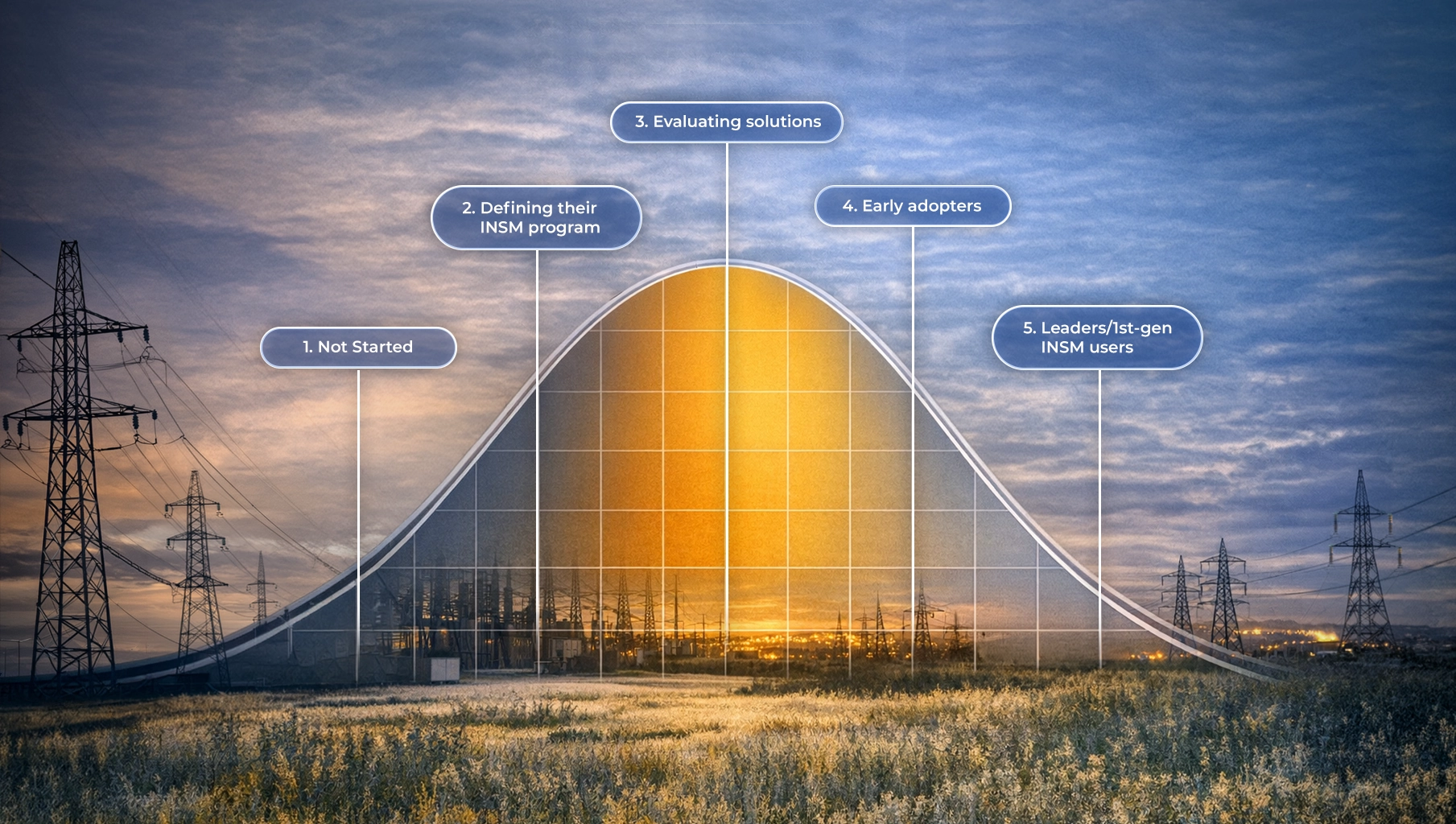
- Not started
- Defining their INSM program
- Evaluating solutions
- Early adopters
- Leaders/1st-gen INSM users
The distribution follows a typical bell curve, with the largest concentration between defining the program and evaluating solutions. That’s healthy. It means organizations are engaging early, asking the right questions and thinking beyond box‑checking. It also means many are realizing that INSM isn’t a single project; it’s a program that evolves.
The early adopters we see are deploying their first INSM solution, which they selected based on CIP-015 requirements. The leaders are especially interesting to engage with now. They have a first- or sometimes even second-generation INSM solution in place that they’re now re-evaluating against the new standard. What makes the utility industry unique, especially within the NERC CIP community, is how leaders and early adopters are so willing to pull the rest of the industry along and share the pitfalls and best practices that they’ve established.
INSM Deployment: Crawl, Walk, Run (and Plan Ahead)
Successful INSM deployments don’t happen overnight. Before even evaluating technology, here are some key considerations.
- Who are the stakeholders that need to be involved in the project?
- Where will you start? Are you going to deploy in your control center, substations, out-of-scope site or lab first?
- Are you going to capture everything and achieve 100% visibility or use a risk-based approach?
- Do you have the infrastructure in place to deploy an INSM?
- Are you going to use network taps, SPAN, RSPAN or ERSPAN?
- How are you going to manage INSM data, including compliance evidence?
- How will INSM fit into your NERC CIP program and security stack (integrations)?
Common Pitfalls to Avoid
Based on real‑world experience working with NERC-regulated utilities across North America, I repeatedly encounter several traps utilities can avoid with the right mindset:
1. Underestimating complexity. This is not just “deploying sensors.” INSM requires coordination across OT, IT, networking, physical security and compliance teams. Expect unknowns — and plan for them.
2. Checklist‑driven compliance. Relying on a prescriptive checklist without understanding the objective of the standard creates gaps and potential audit exposure later.
3. Ignoring data management. We discussed the central role of data management for CIP-015 in our first webinar, captured here. Retention, retrieval, reporting and audit evidence matter. If you can’t efficiently produce PCAPs and logs, compliance becomes painful fast.
4. Waiting too long to begin. Design cycles, procurement, supply chain delays and staffing constraints all add up. Starting late almost guarantees stress.
Final Recommendations for NERC CIP-015-1 and 015-2
If I had to distill everything we’re seeing into a few recommendations, they would be these:
- Start now. Deadlines are closer than they appear when you factor in real‑world constraints.
- Focus on objectives, not just compliance. INSM should strengthen security posture, not just satisfy auditors. You’ve got to run this program for a long time, so you want to design it correctly up front.
- Plan for CIP‑015‑2 even if it’s not fully ratified yet. Many architectural decisions made today will be difficult to undo later.
Lastly, choose partners, not just products. Experience matters. I spent most of my career as a customer, not a vendor, and I sometimes discounted the value of a true partnership with my vendors, especially early in my career. When you’re faced with challenging new requirements like these, you want vendors you can rely on to help you address them.
For more information about anything discussed here, be sure to watch the webinar replay. Or contact us to set up a meeting with me or another one of our NERC CIP experts. We're here to help you.

.webp)