North American electric utilities and independent power producers (IPPs) are entering a pivotal period as NERC CIP‑015, the new internal network security monitoring (INSM) reliability standard for high and medium impact Bulk Electric System Cyber Systems (BES), moves from planning to reality. CIP-015 recognizes a reality that utilities have long grappled with: visibility into internal networks can no longer be optional. It’s essential for detecting lateral movement, identifying anomalous traffic and responding to modern cyber threats that bypass traditional perimeter defenses.
Over the past two decades I’ve worked for a number of utilities where I’ve developed, managed and executed NERC CIP programs for both medium and low impact BES. I’ve also been deeply involved in the development and interpretation of INSM. You could say this is not only my area of expertise but also my passion.
To help the industry navigate this shift, Nozomi Networks has launched a webinar series focused on the real-world experiences, challenges and lessons learned from early adopters. Various Nozomi and other industry experts are joining me throughout the series to share their knowledge and passion, too, while unpacking the toughest aspects of the standard and answering your questions. This and subsequent blog posts will capture the key insights from each episode.
The first episode covered how utilities are approaching INSM deployments, what issues they’re running into and our recommendations for tackling them.
Common Pitfalls
In our conversations with utilities and IPPs as they prepare for INSM, we see several recurring mistakes. They tend to fall into three buckets: compliance burden, program development and implementation complexity. Here are some of the biggest issues.
1. Treating INSM as a technical project instead of a program
Many utilities underestimate INSM by approaching it as a single deployment rather than an ongoing operational capability. Too often they jump into tooling before defining:
- Key stakeholders
- Monitoring methodology
- Detection approach and scope
- Evidence management workflows
- Roles and responsibilities
- Longterm data handling expectations
Developing a program is about focusing on people. process and technology. Overlooking any of these leads to rework and gaps during audits.
2. Underestimating the data management challenge
CIP-015 compliance isn’t just about sensor deployment to gain east-west visibility within a network. It’s about data management.
Implementing INSM means ingesting vast amounts of network telemetry. But collecting that data is only the beginning. Utilities must analyze it, contextualize it and then manage the evidence associated with monitoring, analysis and response. INSM turns on the spigot at full force. You’ll be dealing with a ton of data coming in on the front end and a ton of data on the back end as you manage evidence. Making sense of that volume requires not just technology but well-defined processes and workflows. Knowing what evidence you need to keep and what can be purged should be well defined within your program.
2a. Starting data collection without a collection strategy
Utilities often begin ingesting traffic and telemetry before deciding what data they really need. INSM produces enormous volumes of traffic metadata, and unplanned ingestion results in:
- Unmanageable datasets
- Unclear evidence chains
- Difficulty scaling to additional sites
- Inefficiencies during investigations
Defining your collection strategy prevents “collect everything chaos.”
2b. Not preparing for the evidence burden
A significant part of CIP-015 is evidence management. It requires:
- Proof of continuous monitoring
- Proof of alert triage and follow up
- Proof that anomalies were addressed
- Proof that policies and procedures are followed
As you build your evidence management process, make sure it aligns with regulatory expectations.
3. Failing to define “anomalous” behavior early
Without a clear, documented definition of anomalous activity within your unique environment, utilities end up with inconsistent responses and unverifiable audit evidence.
Be sure to define:
- What is an anomaly?
- What is a deviation?
- How will deviations be detected (baseline, behavioral, IOC, etc.)?
- How will deviations be analyzed?
4. Assuming maturity will “come later”
Utilities sometimes believe they can deploy sensors first and “mature over time.” INSM enforcement deadlines require operational maturity, not just having technology in place. This includes:
- Documented procedures
- Defined roles
- Repeatable workflows
- Ongoing reporting
- Personnel training
- Governance structures
Utilities that build these components early will be in a far better position when enforcement arrives.
5. Underestimating the value of a mock audit
Skipping a dress rehearsal audit, especially for a new regulation, increases the risk of fines. A mock audit exposes:
- Missing documentation
- Unclear decision logic
- Gaps in evidence storage
- Uncertainty among personnel
- Contradictions between process and practice
Ahead of the audit, document workflows and methodologies so teams respond consistently and auditors can trace your logic.
Enforcement Deadlines vs. Readiness
As an industry, we’ve known this is coming, but 1:1 conversations with owners and operators reveal uneven familiarity with the standard and whether it applies to them, even among high and medium impact BES Cyber systems. Our two webinar poll questions confirmed this.
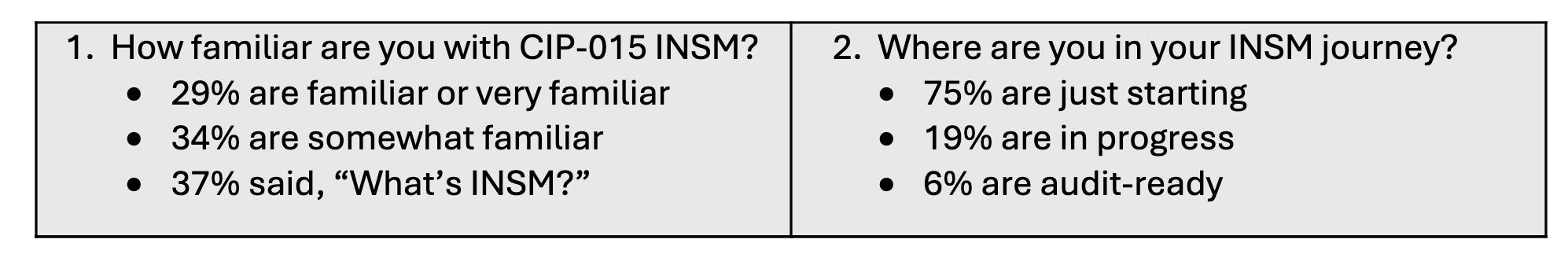
At first blush, the poll results aren’t surprising given enforcement timelines:
- October 1, 2028: Enforcement begins with high and medium impact BES, particularly control centers with External Routable Connectivity (ERC). While more than two years away, this deadline requires utilities to move from conceptual planning to operational readiness now. That means defining your INSM scope and assets, identifying network data feeds, selecting tools and an operating model, and building evidence and governance processes.
- October 1, 2030: Further down the road, enforcement expands to include all other high and medium impact BES. This later deadline provides slightly more runway, but the scale of the requirements means these utilities should also be thinking ahead now. Achieving full operational maturity at enterprise scale takes time, coordination and iteration.
Three Practical Steps to Get Started
Even if enforcement dates seem distant, utilities that delay will face compressed timelines and logistical bottlenecks, especially when it comes to scaling INSM across multiple sites or regions.
Here are three steps you should take now:
1. Assess CIP-015 scope and applicability.
Gain an understanding of what sites, systems and networks are in scope of the new standard. Document what you already monitor internally, where gaps exist and which network segments have no monitoring at all.
2. Align stakeholders.
INSM compliance spans cybersecurity, operations, engineering, compliance and leadership teams. Misalignment early on leads to costly rework later.
3. Evaluate INSM solutions holistically.
The focus on this webinar and blog series isn’t INSM products, and we won’t be touting the specifics of our platform. But technology is a key component of your program. As you evaluate vendor solutions, pay attention not only to how each solution covers the CIP-015 requirements but also:
- Flexibility across different network architectures
- Ease of deployment and management
- Integration with existing tools and processes
- Total cost of ownership, not just purchase price
Because INSM is a long-haul program, sustainability matters as much as functionality.
Want More Advice? Reach Out for a Meeting.
The FERC journey to requiring INSM for BES has been long and complex, with evolving threats and prior CIP standards paving the way for CIP‑015. While the requirement may feel new, the concepts behind it have been in circulation for years. As INSM moves closer to enforcement, utilities that invest now in visibility, data management, workflow definition and cross-team coordination will be positioned for success.
Tune in to each webinar episode, either live or recorded, for answers to your questions. Or contact us to set up a meeting with one of our NERC CIP experts. We're here to help you.