The Nozomi Networks Labs team has discovered, researched, and disclosed a series of vulnerabilities found on the Advantech TPC-110W HMI, also sold under the brand name CtrlX HMI WR21 by Bosch Rexroth. These vulnerabilities, ranging in severity from CVSS scores of 7.3 to 8.8, have the potential to totally compromise this HMI. When chained together, the vulnerabilities described below have several real-world impacts across multiple sectors, allowing threat actors to gain access to forbidden capabilities such as malware installation, HMI shutdown or to use the device as an interface to reach other systems or networks in the facility.
Beyond exploiting and compromising this piece of equipment, security flaws allow for a malicious threat actor to execute arbitrary code on the operating system of the HMI, and to pivot access into the rest of the network. In this blog, we briefly introduce HMIs, both traditional and web based, then discuss specifics related to the Advantech TPC-110W. We cover 9 vulnerabilities discovered during our research, along with their impacts, attack scenarios, and recommended mitigations.
In response to our findings, Advantech, supported by Bosch Rexroth, addressed all reported vulnerabilities, patching them with a specific firmware release.
What are HMIs?
A Human-Machine Interface (HMI) is a specialized component (can be a hardware or software interface) used in industrial automation and control systems to facilitate communication between humans and machines. They are particularly used in manufacturing and process control environments. HMIs are designed to provide real-time data, control, and monitoring capabilities for operators and engineers, allowing them to interact with and manage controllers, equipment, machinery, and processes. Key features of an industrial HMI typically include data visualization, process control, data acquisition and alarm notification. HMI devices are usually installed in a wide range of critical facilities, physically accessible by many workers at a time.
Many new HMIs offer browser-based interfaces that are easy to implement, maintain and develop. However, the security posture of this kind of HMI should be adopted through the implementation of a set of security configurations. These security configurations are typically enforced through a kiosk mode, preventing the user interacting with the HMI from performing forbidden operations such as settings modification or shutdown of the HMI itself.

The Advantech TPC-110W HMI
The Advantech TPC-110W HMI device, also sold by Bosch Rexroth under the brand name ctrlX HMI WR21, offers a browser-based graphical interface to monitor and interact with remote systems. This full-featured web browser is the main interface available for users, designed to be reached through a web-based communication (HTTP or Web Socket).
This HMI is an Android-based device that comes with a pre-installed Chromium web browser and a configurable kiosk mode application. This kiosk mode configuration helps segregate privileges that should be accessible only to administrators, such as changing the settings of the HMI, shutting down the system or installing additional applications. As explained in the user manual, the HMI supports the installation of third-party Android applications in order to add new functionalities to the device.
Figures 2 and 3 respectively show the password setup required to exit from the kiosk mode and the configuration menu provided to start the Chromium browser as the main graphical interface.


The Advantech TPC-110W HMI is designed to be controlled remotely. This capability is implemented with a specific Android application named Android Agent (package name com.adv.client), preinstalled on the operating system. This application runs with high privileges, to allow a remote administrator to perform specific operations on the device such as enabling the debug interface or remote login through VNC and installing or removing applications.
The Android Agent application requires the user to specify a server to establish a connection allowing the administrator to perform operations on the HMI remotely. The server-side infrastructure is provided by Advantech through a cloud-based service called AppHub. AppHub server settings can be set up in three different modes:
- Specifying a server manually
- Importing a configuration file
- Scanning a QR code
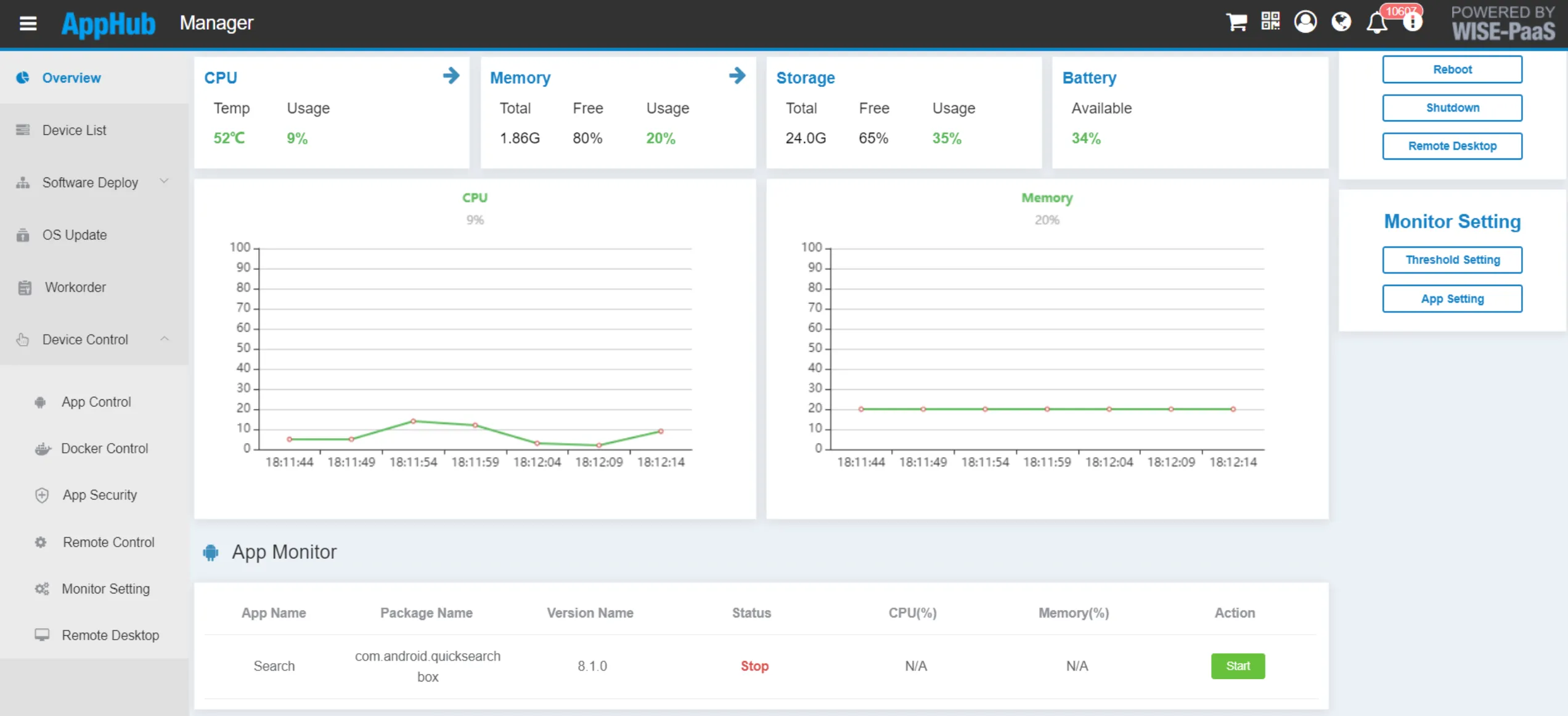
Once the connection between the Android Agent application and the AppHub server is established, a remote administrator can manage the HMI device through the cloud-based Advantech service. As described in the official AppHub documentation, the Android Agent application is publicly available for download.
Figure 4 shows the main interface of the Android Agent application and Figure 5 the cloud-based AppHub device management interface. Since the Android Agent application provides high-level privileges and the ability to control the HMI remotely, this software layer represents an attractive access vector to research and analyze.

Advantech TPC-110W Vulnerabilities
During our research phase, Nozomi Networks Labs analyzed the latest Android build available for the Advantech TPC-110W HMI device (QQ3A.200805.001) shipped with a preinstalled Android Agent application (version21222.fe0bc0f.20220125).
Below is a list of all 9 high risk vulnerabilities discovered by Nozomi Networks Labs.
High risk
- CVE-2023-45844: Improper Access Control (CWE-284), CVSS v3.1 Base Score 7.3 (CVSS:3.1/AV:P/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H)
- CVE-2023-41255 Improper Authorization (CWE-862), CVSS v3.1 Base Score 7.9 (CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:C/C:L/I:H/A:L)
- CVE-2023-43488: Missing Authentication For Critical Function (CWE-306), CVSS v3.1 Base Score 8.8 (CVSS:3.1/AV:A/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H)
- CVE-2023-41960: Improper Export of Android Application Components (CWE-926), CVSS v3.1 Base Score 7.1 (CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:H/A:H)
- CVE-2023-41372: Use of Hard-coded Credentials (CWE-798), CVSS v3.1 Base Score 7.8 (CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H)
- CVE-2023-45220: Missing Authentication For Critical Function (CWE-306), CVSS v3.1 Base Score 8.8 (CVSS:3.1/AV:A/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H)
- CVE-2023-45321: Cleartext Transmission of Sensitive Information (CWE-319), CVSS v3.1 Base Score 8.3 (CVSS:3.1/AV:A/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:L)
- CVE-2023-45851: Missing Authentication For Critical Function (CWE-306), CVSS v3.1 Base Score 8.8 (VSS:3.1/AV:A/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H)
- CVE-2023-46102: Use of Hard-coded Credentials (CWE-798), CVSS v3.1 Base Score 8.8 (VSS:3.1/AV:A/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H)
Impacts and Attack Scenarios
As mentioned, the Advantech TPC-110W HMI device is designed to be physically accessible to multiple users, offering the Chromium web browser as the main graphical interface, securely configured through the kiosk mode.
With this configuration enabled, a malicious user with physical access to the HMI, exploiting the vulnerabilities listed above, can acquire full access to the HMI device bypassing the kiosk mode within the Chromium browser interface. This would allow the attacker to gain access to forbidden capabilities such as installing malware, shutting down the HMI or using the device as an interface to reach other systems or networks in the facility.
Attacking the Operating System
Chaining specific vulnerabilities, it is possible to define two different ways to compromise the HMI device interacting with the Chromium browser. The root for both the paths is CVE-2023-45844, an Improper Access Control vulnerability affecting the Chromium browser. Despite the kiosk mode configuration, by leveraging this vulnerability a malicious user can abuse the Chromium browser itself to install an external attacker-controlled application on the HMI, gaining the ability to execute arbitrary code on the operating system. Figure 6 shows the installation of an application through Chromium as an example.

Since the Advantech TPC-110W HMI is an Android-based device, this is not enough to completely compromise the system, since the Android security model allows third party applications to run only with low privileges on the system (application sandbox). This is where the other vulnerabilities come into scope.
The first exploitation path leverages two vulnerabilities that are related to weak configurations of the customized Android operating system installed on the HMI device, specifically CVE-2023-41255 and CVE-2023-43488. CVE-2023-41255 is an Improper Authorization vulnerability arising from the fact that one important component of the Android security model, called SELinux, has been disabled. This allows a third party installed application running with low privileges to modify security-relevant system settings.
The second CVE, CVE-2023-43488, is a Missing Authentication For Critical Function vulnerability related to the Android debug interface (ADB) service on the HMI. This capability is a standard feature for Android-based devices and allows administrator users to connect to the system to perform maintenance activities. On the Advantech TPC-110W HMI device, the ADB debug interface is configured to give maximum privileges to administrators that connect to it (logging in with root user) without enforcing any authentication, unsafely exposing this functionality to an attacker. The Android operating system normally allows to interact with the ADB debug interface just physically attaching a USB cable, but this limitation can be removed modifying a specific system security setting and this is where the previously described CVE-2023-41255 vulnerability come into scope.
By chaining CVE-2023-45844, CVE-2023-41255 and CVE-2023-43488 together, we obtained a serious exploitation flaw:
- The attacker installs a malicious application on the operating system abusing the Chromium browser configured in the kiosk mode (CVE-2023-45844).
- Due to the lack of the SELinux enforcement, the malicious application applies a new system setting to expose the ADB debug interface on the network (CVE-2023-41255).
- Due to the lack of credential authentication, the attacker can now connect to the ADB service through the network without the need to physically plug in a USB cable (which is typically impossible without unmounting the device). This allows for a privilege escalation of any user with access to root user on the device (CVE-2023-43488).
After completing these steps, the attacker has gained full access to the HMI device.
Attacking the Android Agent System Application
The second exploitation path exploits several vulnerabilities that Nozomi Networks Labs has found on the Android Agent system application, developed by Advantech in order to allow for remote management of the TPC-110W HMI through their cloud-based platform called AppHub.
The Android Agent application exposes a functionality that allows changes to its configuration data without any authentication, resulting in an Improper Export of Android Application Components vulnerability (CVE-2023-41960).
The configuration data is received by the Android Agent application through an Android Intent (Android-specific communication mechanism), whose payload must be encrypted with a specific key in order to be regularly processed. Our analysis revealed that this encryption key is hard-coded inside the application itself (publicly available for download). This allows an attacker to download it and forge a malicious Android Intent sent to the Android Agent application. This leads to an unauthorized modification of the Android Agent application configuration. We reported this vulnerability as CVE-2023-41372 (Use of Hard-coded Credentials).
The last part of the exploitation process is related to the communication between the Android Agent application and the Advantech AppHub cloud service. As explained above, the user needs to specify the AppHub server IP address in order to set up proper communication with the cloud service. By analyzing the client-server communication, our team discovered several vulnerabilities, some of which are useful to complete the exploitation flow:
- The client-server communication is based on the MQTT protocol, but MQTTS is not enforced.
- The AppHub server can send commands to be executed to the Android Agent application through encrypted MQTT messages, but the encryption key is retrievable in the Android Agent application itself.
The lack of the adoption of MQTTS in place of MQTT does not allow the client Android Agent application to authenticate the AppHub service, accepting any user provided address as a trusted server. Furthermore, the use of a hard-coded key to encrypt exchanged messages allows an attacker to retrieve and leverage it to forge valid commands that will be processed by the Android Agent application. These flows have been reported as CVE-2023-45220 (Missing Authentication For Critical Function) and CVE-2023-46102 (Use of Hard-coded Credentials).
By chaining all the described vulnerabilities, it is possible to compromise the Android Agent application and, consequently, the TPC-110W HMI device, allowing arbitrary execution of high privileged commands through the Chromium browser configured with the kiosk mode, intended to be secure to multiple users without administrative privileges. To recap, below are the chained vulnerabilities and exploitation detailed above:
- The attacker installs a malicious application on the operating system, abusing the Chromium browser locked by the kiosk mode (CVE-2023-45844).
- The installed malicious application forges and sends an Android Intent to the Android Agent application changing its configuration, specifying an attacker-controlled IP address server replacing the trusted AppHub server (CVE-2023-41960 and CVE-2023-41372).
- After the reception of the malicious Android Intent, the Android Agent application connects to the attacker-controlled server and sets up a valid connection due to the lack of a proper authentication mechanism (CVE-2023-45220).
- The attacker forges encrypted messages and sends them from the controlled server to the Android Agent application to execute privileged operations on the HMI device (CVE-2023-46102).
Figure 7 shows the exploitation flow that leads to the compromise of the TPC-110W HMI device through the Android Agent application. As a result, the attacker can abuse all of the functionalities implemented in the Android Agent application such as enabling the ADB debug interface on the device, accessing the device enabling VNC remote protocol, installing and removing applications, and finally executing arbitrary shell commands with high privileges – administrative or root user.

Recommended Mitigations
Bosch Rexroth released an official security advisory describing the list of vulnerabilities, the affected products and related firmware versions. Customers and asset owners must upgrade their devices following the instructions provided by official advisory to prevent unauthorized access and exploitation to the HMI devices in use.
HMIs are an attractive target in industrial environments and an increasingly significant component for research due to the interconnectivity of industrial networks and the potential risks that come with compromise: unauthorized access, data breaches, malware and viruses, Denial of Service attacks and physical security. We urge customers and asset owners to follow the recommended remediation described in the official Bosch Rexroth security advisory.









