This article was updated on March 3, 2020.
It has been reported today that Norsk Hydro either switched to manual mode or temporarily stopped aluminum production at several plants following a cyberattack. The Norwegian National Security Authority and local media in Norway describe the incident as a ransomware attack by a malware called LockerGoga. The attack has apparently brought the company’s IT systems to a standstill.
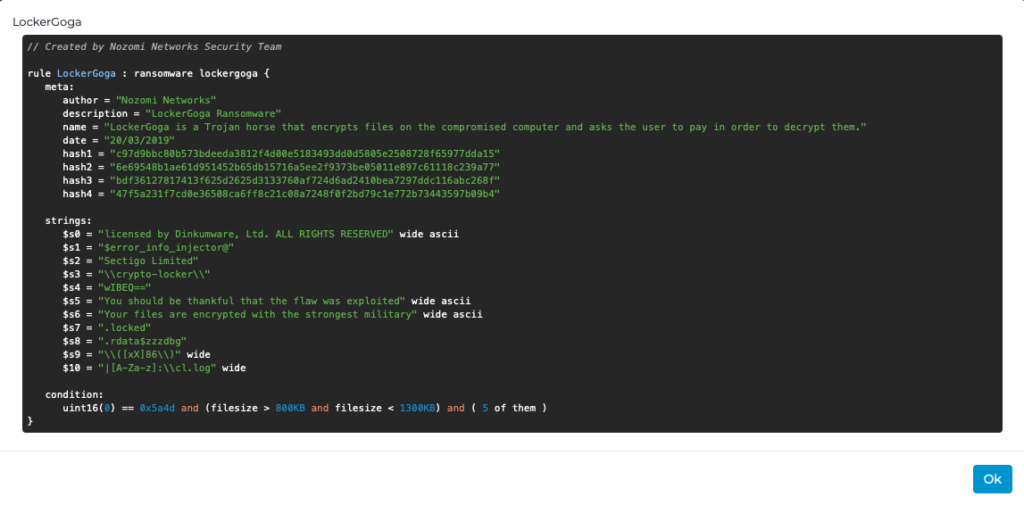
Given the significance of this attack, Nozomi Networks Labs has conducted a preliminary evaluation of LockerGoga. Read on to learn about this ransomware and our research team’s assessment of it.
Ransomware Attack Impacts Aluminum Production
According to media reports, the malware attack began on the evening of Monday, March 18th, 2019 Oslo time (UTC + 1). On March 19th, 2019, the company’s website was not available and production impacts had been reported:
- Potlines, which monitor molten aluminum, and need to be kept running 24 hours a day, had been switched to manual mode
- Some factories have been forced to halt production
- Several metal extrusion plants have been closed
- At certain facilities, some computer systems are unavailable, and printed orders are being fulfilled
- Power plants are functioning normally
- No safety-related incidents have been reported
Updated March 22, 2019: What is the LockerGoga Ransomware?
Nozomi Networks Labs has conducted a preliminary analysis of a LockerGoga sample with the SHA256:
6e69548b1ae61d951452b65db15716a5ee2f9373be05011e897c61118c239a77
The ransomware can encrypt files with any of the specific extensions listed below:
doc, dot, wbk, docx, dotx, docb, xlm, xlsx, xltx, xlsb, xlw, ppt, pot, pps, pptx, potx, ppsx, sldx, pdf
We have also analyzed the latest version of the LockerGoga sample with the SHA256:
c97d9bbc80b573bdeeda3812f4d00e5183493dd0d5805e2508728f65977dda15
This version is likely the one that targeted Norsk Hydro. It encrypts files with these extensions:
.doc, .dot, .docx, .docb, .dotx, .wkb, .xlm, .xml, .xls, .xlsx, .xlt, .xltx, .xlsb, .xlw, .ppt, .pps, .pot, .ppsx, .pptx, .posx, .potx, .sldx, .pdf, .db, .sql, .cs, .ts, .js, .py
The extension types indicate that the main goal of the threat actor is to encrypt files containing important data for users. In fact, at the end of the encryption phrase, a file called README_LOCKED.txt is dropped inside the filesystem containing the following message:
Greetings!There was a significant flaw in the security system of your company.You should be thankful that the flaw was exploited by serious people and not some rookies.They would have damaged all of your data by mistake or for fun.Your files are encrypted with the strongest military algorithms RSA4096 and AES-256.Without our special decoder it is impossible to restore the data.Attempts to restore your data with third party software as Photorec, RannohDecryptor etc.will lead to irreversible destruction of your data.To confirm our honest intentions.Send us 2-3 different random files and you will get them decrypted.It can be from different computers on your network to be sure that our decoder decrypts everything.Sample files we unlock for free (files should not be related to any kind of backups).We exclusively have decryption software for your situationDO NOT RESET OR SHUTDOWN – files may be damaged.DO NOT RENAME the encrypted files.DO NOT MOVE the encrypted files.This may lead to the impossibility of recovery of the certain files.The payment has to be made in Bitcoins.The final price depends on how fast you contact us.As soon as we receive the payment you will get the decryption tool andinstructions on how to improve your systems securityTo get information on the price of the decoder contact us at:DharmaParrack@protonmail.comwyattpettigrew8922555@mail.com
The LockerGoga malware encrypts many file types and presents its ransom demands in the README_LOCKED. text file.
This note is from the latest version of the ransomware, most likely the version that targeted Norsk Hydro.
The message states that in order to get the files back, the user is forced to pay a ransom using the cryptocurrency Bitcoin.
How Does LockerGoga Work?
The malware encrypts files with the targeted extensions and then drops the ransom note in the filesystem, informing users about the steps required to get the files back. This is a classic approach used by most ransomware malware.
The malware does not have the capability to spread to other targets, but it does appear to use some anti-analysis techniques to avoid detection by security analysts. For example, it seems to detect the presence of a Virtual Machine and has the capability to delete itself from the filesystem in an effort to avoid sample collection.
Because the threat actors did not add any custom or complex capabilities to the malware code (C&C, DNS beaconing, etc.), we can assume that its intended impact is disruption, rather than espionage.
Some researchers have suggested that the attackers may have used Active Directory as a mechanism for spreading the malware. A possible scenario (confirmed by NorCERT):
- The threat actors were able to infect a system that was registered in the Domain Admin Group of the target organization
- The malicious executable was placed in the Netlogon directory so that it could be automatically propagated to every Domain Controller
- Many firewalls accept Active Directory information by default
Update March 20, 2019: Multiple LockerGoga Samples
In the last 24 hours the Nozomi Networks Labs team has obtained four different LockerGoga samples. The multiple samples are an indicator that the ransomware is under active development.
Analyzing the samples reveals:
- After execution, the malware moves itself to the directory %TEMP% in order to cover the malicious activity.
- The samples are not obfuscated and do not implement any anti-analysis techniques.
- The file containing the ransom note is stored in the Desktop folder and has different filenames depending on the sample. Using different hardcoded file names for each malware sample represents an attempt to bypass security solutions which rely on checking filenames created inside a system.Some observed filenames are: READ-ME-NOW.txt, README-NOW.txt and README_LOCKED.txt. It is highly probable that more filenames used in other variations of the malware exist in the wild.
- The extensions used to decide which files to encrypt are slightly different among different version of the samples. In some cases, we observed that the malware also encrypts .exe and .dll files. This increases the impact on the victim’s system because it encrypts Windows core files as well.
- All the samples run independently, without the need to connect to outside servers.
These aspects indicate that LockerGoga is a classic ransomware malware. There is no functionality targeted at ICS specific devices or protocols, despite some of Norsk Hydro’s production being affected.
How to do you know if you’re infected with LockerGoga? How do you get rid of it?
You can identify an infection because the targeted files will be encrypted and the file extension “.locked “ will be appended at the end of the filenames.
Currently, the only known way to remove LockerGoga from your system is to restore from backup.
For Nozomi Networks customers, our Threat Intelligence has been updated to include the capability to detect the LockerGoga malware.
Norsk Hydro Utilizes Innovative Communications Outreach as Part of Incident Response
Unlike many companies who didn’t reveal that they were subject to a cyberattack for an extended period of time, Norsk Hydro has taken a completely different approach. They quickly created a live stream briefing on the attack and are providing regular updates on their Facebook channel.
Attacks on Industrial Systems Are Reality, Not Fantasy
The attack on Norsk Hydro is just the latest to hit the industrial sector, carrying the potential for a significant financial impact. Other examples include:
- In 2012, a malware attack cost Saudi Aramco approximately $1 billion in recovery efforts and required replacement of 35,000 damaged computers.
- The 2017, the NotPetya attack resulted in $10 billion in damages to supply chain companies worldwide, according to the White House. For example, costs to the pharmaceutical company Merck were pegged at $870 million.
To minimize the chance that your system will be impacted by LockerGoga, we suggest:
- Ensuring your systems have current and working back-ups
- Communicating with employees about ways to recognize a phishing email, and what to do if they think they received one
- Monitoring your systems with solutions that rapidly identify malware, indicators of compromise and behavioral anomalies
I urge you to stay tuned for further updates on LockerGoga. Subscribing to Nozomi Networks Labs notifications, via the link below, will ensure that you receive updates on this and other important Nozomi Networks Labs research.










