In December 2021, as most people were looking forward to a quiet end of the year, Log4Shell, the vulnerability in the Apache Log4j logging utility, burst onto the scene. The combination of relatively easy remote code execution and widespread use of the Apache Log4j utility made this vulnerability extremely newsworthy, demanding all hands on deck from security teams. Nozomi Networks Labs published a blog in December of 2021 with an early dissection of the vulnerability as well as an in-depth analysis of the Muhstik botnet that sought to exploit Log4Shell.
As with most big zero-days, Log4Shell received a large amount of coverage as it unfolded. In this blog, we would like to take things a step further and highlight additional tools and insights from Nozomi Networks that provide long-term security after the dust settled around Log4Shell.
Identification Can Be as Important as Detection
During the initial discovery period, IOCs (Indicators of Compromise) were released to allow security teams to identify suspicious traffic that may be related to a Log4Shell exploit. While this is extremely helpful when fighting a new exploit, it can be a manual and somewhat time-consuming process for security teams that are already stretched thin. The first step Nozomi Networks took was to develop packet rules tied to CVEs (Common Vulnerabilities and Exposures) associated with the Log4Shell vulnerability. It’s a lot easier to have an alert show up saying that a communication containing a payload was detected, indicating an attempt to exploit Log4Shell, than to piece together the attack from multiple IOCs strung together.
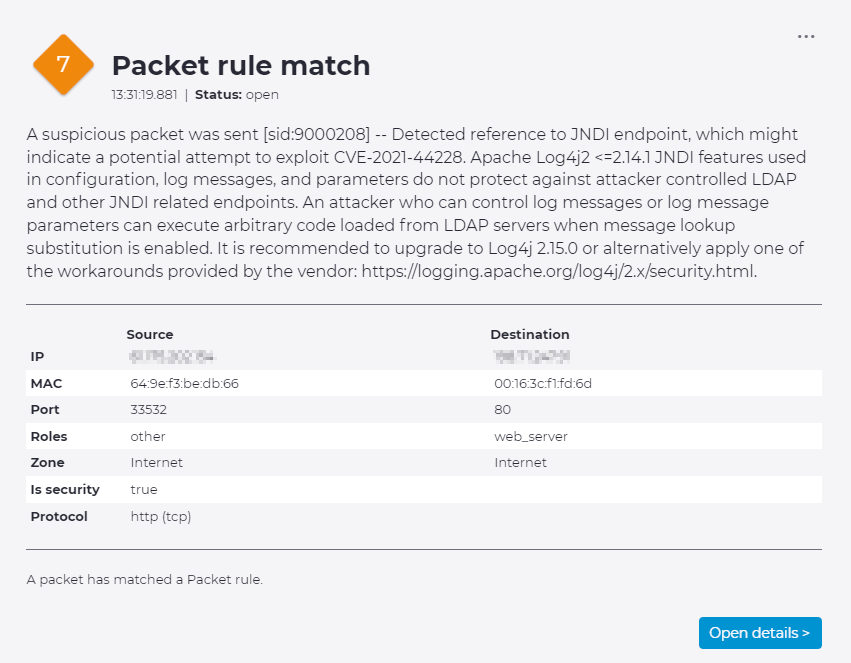
A small sample of the content rules released around Log4j:

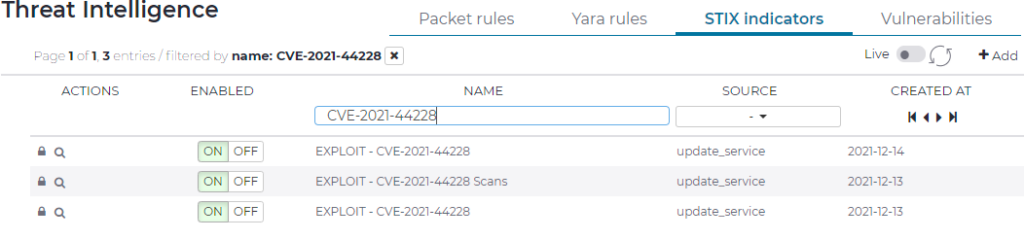
Of course, packet detection is the tip of the iceberg when it comes to exploits. For every single active exploit, there may be hundreds of systems that are vulnerable to being exploited. This is even more of an issue when dealing with OT environments that may have limited connectivity (an offshore platform, a pipeline monitoring system, an air-gapped refiner, etc.) where a vulnerability may be exploited long after the initial rush to contain a zero-day has passed. To continue improving protection against Log4j, Nozomi Networks Labs utilizes our Asset Intelligence subscription to help highlight systems with vulnerable Apache libraries. We recommend combining this with the Smart Polling feature that will selectively poll Windows and Linux while not disturbing sensitive OT assets on the same network. Using this information, security teams can quickly identify vulnerable assets in their environment and put proper protections in place (such as selective blocking on firewall or IPS rulesets) while they rolled out the appropriate patches.
Sharing Detection Strategies
SOC and NOCs (Security/Network Operations Centers) don’t contain an array of screens just for watching World Cup matches. Security teams need an “at a glance” method for quickly assessing risk in the environment. Nozomi Networks recently released a feature called “Content Packs” which allow for quickly sharing queries and dashboards with the community at large for a common threat or shared process. The Labs team put together a Content Pack to be able to quickly share queries specifically related to the Log4Shell attack.

Once queries have been created, it is a simple matter to export those queries as a .json file to share with others. It is important to understand that these are simply the queries themselves and contain no data specific to a customer’s environment. For example, the Log4j Content Pack .json file reads:
[[{"e":"query","h":350,"w":6,"opts":{"query":"alerts | where threat_name include? CVE-2021-44228 | group_by name | pie name count","description":"log4j - Pie Chart for Stix Indicator hits"}},{"e":"query","h":400,"w":6,"opts":{"query":"alerts | where trigger_id == 2034649 OR trigger_id == 2034650 OR trigger_id == 2034651 OR trigger_id == 2034652 OR trigger_id == 2034653 OR trigger_id == 2034654 OR trigger_id == 2034656 OR trigger_id == 2034657 OR trigger_id == 9000208 OR trigger_id == 9000209 | group_by ip_src | pie ip_src count","description":"log4j - Packet Rule hits - Pie Chart with Attacker IP"}},{"e":"query","h":400,"w":6,"opts":{"query":"alerts | where trigger_id == 2034649 OR trigger_id == 2034650 OR trigger_id == 2034651 OR trigger_id == 2034652 OR trigger_id == 2034653 OR trigger_id == 2034654 OR trigger_id == 2034656 OR trigger_id == 2034657 OR trigger_id == 9000208 OR trigger_id == 9000209 | group_by ip_dst | pie ip_dst count","description":"log4j - Packet Rule hits - Pie Chart with Victim IP"}},{"e":"alerted-nodes-number","h":350,"w":3,"opts":{}},{"e":"query","h":350,"w":12,"opts":{"query":"alerts | where trigger_id == 2034649 OR trigger_id == 2034650 OR trigger_id == 2034651 OR trigger_id == 2034652 OR trigger_id == 2034653 OR trigger_id == 2034654 OR trigger_id == 2034656 OR trigger_id == 2034657 OR trigger_id == 9000208 OR trigger_id == 9000209","description":"log4j Packet Rule hits"}},{"e":"query","h":350,"w":12,"opts":{"query":"alerts | where threat_name include? CVE-2021-44228","description":"log4j Stix Indicator hits"}}]]

While you can build these queries yourself, it is much easier to simply drag and drop the .json file into the import window and start using it immediately. More importantly, it allows Nozomi Networks Labs to quickly share content around new threats without the need for an update or even a direct connection to the internet. Of course, this feature can be easily used by our customers to share queries internally or externally with the larger community.
So, while it’s important to highlight early detection of new threats, it’s also important to have a plan for dealing with them in the long term. Zero-day detection is fantastic, but it’s only a part of what security teams are dealing with on a daily basis. Once the threats have been identified, tracking vulnerable systems and showing progress on reducing the risk to the network becomes another full-time job. The big headline zero-days like Log4j are only the beginning for cybersecurity professionals and with the addition of content packs, Nozomi Networks looks to increase the speed at which detection and prevention strategies can be shared.










