Not long after our blog discussing detecting Log2Shell activity in your network with a content pack, Industroyer2 reared its ugly head. Nozomi Networks Labs dug deeply into the topic of Industroyer2 through various blogs sharing technical details of the exploit and an in-depth White Paper providing insight into the evolution of Industroyer2 and the campaign behind its spread. As part of their Industroyer2 research efforts, Nozomi Networks’ security research and product development teams put together a content pack to help our customers look for activity related to Industroyer2 in their network. While there have been no reports of Industroyer2 out in the wild, it’s not a stretch of the imagination to expect some variant of this exploit in circulation soon.
As a quick refresher for those not familiar, a content pack is a way of exporting a combination of queries and reports into a single JSON file that can be exported into a completely separate environment. At their core, content packs are just instructions for executing queries and reports, so they do not contain any proprietary information and are safe to share. This allows for Nozomi Networks customers to quickly share custom reports or queries internally or to the Nozomi Networks user community. Content packs can be used to share things like best practices between organizations in similar industries or, in this instance, sharing detection strategies for new threats.
Getting Started with the Industroyer2 Content Pack
After downloading (and extracting the .json file) the content pack from Nozomi Networks, go to the “Administration” page in Guardian and select “Import.”
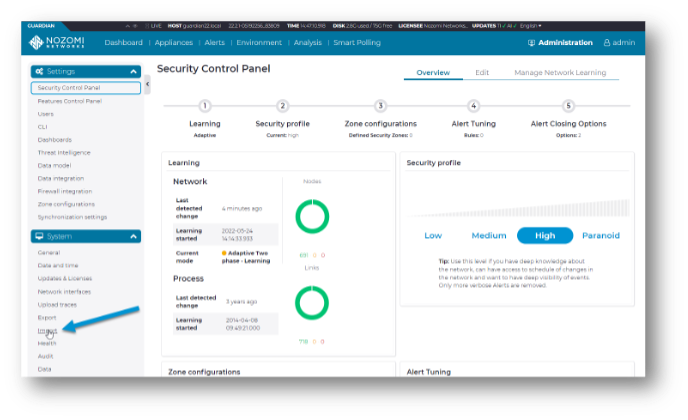
Then just drag and drop the .json file into the appropriate box at the bottom of the page.

Figure 2. Importing the content pack.

Once the content pack has been imported, you will see a report folder and query group containing the newly imported content. Navigating to Analysis > Queries > Saved queries page will now show a “Content Pack Industroyer2” query group.

Selecting the “Content Pack Industroyer2” group from the dropdown will bring you to a page with all of the new queries.
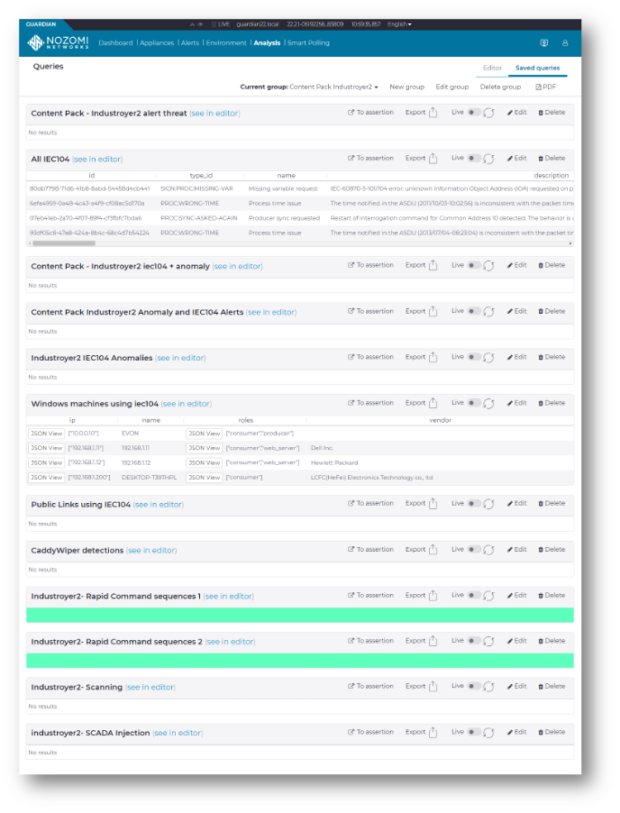
The queries should be executed automatically when you open the group. If not, click on “Edit” and then select “Automatically execute queries on load” to enable this.

Behind the Queries
Hopefully you will find some of the queries returning with no results, meaning you don’t have an infestation of Industroyer2 running rampant through your network. However, it is important to remember that the Industroyer2 malware is a single piece in a larger attack against an industrial environment, so there are several things to watch for when threat hunting.
Aside from looking for signatures matching Industroyer2 specific alerts, we need to expand our search to cover traffic patterns that may be either an indicator of an Industroyer2 copycat or a precursor to an infestation. Let’s walk through each of the queries in this content pack:
- Content Pack – Industroyer2 alert threat – This query looks for instances of signature detections of Industroyer2.
- All IEC104 – This query highlights all alerts triggered where the protocol involved is IEC 104, as this was the protocol hijacked by Industroyer2. From a threat hunting perspective, it is good to look for alerts that may be “adjacent” to the main threat as they could be indicators of compromise (IOC) or highlighting a problem that needs to be addressed to prevent exploitation.
- Industroyer2 IEC104 + anomaly – This looks for anomalous traffic behavior in IEC 104 traffic that could indicate a potential event.
- Industroyer2 anomaly and IEC104 alerts – Similar to the previous query, this is highlighting IEC 104 anomalous alerts and sorting by source IP address.
- Industroyer2 IEC104 anomalies – similar to the previous two queries, but highlighting the timeframe. Providing three individual queries that sort by different criteria allows for a quicker bird’s eye view, providing threat hunters with all the information they need in a readily accessible form.
- Windows machines using IEC104 – This query can help isolate Windows systems that are transmitting traffic using IEC 104. It is important to verify that all the machines showing up in this query are supposed to be using IEC 104 and are not systems that have been infected and are attempting to spread malware.
- Public Links using IEC104 – This query will highlight any systems that are using IEC 104 to communicate with an address outside of the internal network, an indicator that there may be a compromise or at least should be further investigated to determine why this communication is taking place.
- CaddyWiper detection – CaddyWiper is a tool that has been used in conjunction with Industroyer2 to wipe data from compromised systems. Its presence most likely indicates a threat actor is operating in your network.
- Rapid Command sequences 1 & 2 – In a typical environment, 99% of the IEC 104 traffic is a READ operation, with very few WRITE commands being sent. These two queries check for more than five commands to the same RTU within a 30 second time frame. This query is prone to false positives and should be fine tuned to your environment by adjusting either the amount of commands or the time frame.
- Industroyer2 scanning – Reconnaissance of the network is a common early stage of an incursion. Care should be taken to look for network scans in your environment.
- SCADA injection – While not necessarily associated with Industoyer2, any tampering with SCADA protocols should be investigated as they could lead to the discovery of other tools used by the Sandworm APT group or other threat actors.
Tying it all Together
In the content pack alongside the queries, you will find an executive report that can be run on a schedule or on demand. This report provides a read out of your environment in a format that can be distributed via email or other means to those who do not have direct access to the Guardian interface. The report goes into detail on each of the detections and provides background information to help the reader better understand the information.
Content packs are a relatively new addition to the tools Nozomi Networks provides our customers to stay informed and protected against new threats. Even better, they were created with sharing in mind, to allow for our global community of customers and partners to better collaborate on defending what is important to their business.