A Note to our Customers and Partners in the Middle East
More InformationCVE-2021-26726
A remote code execution vulnerability affecting a Valmet DNA service listening on TCP port 1517 allows an attacker to execute commands with SYSTEM privileges
An un-authenticated network user can craft specific packets targeting a Valmet DNA service, listening by default on TCP port 1517. By exploiting a predictable encryption key, the attacker can trigger commands that will be executed on the remote machine with the SYSTEM privileges.
February 16, 2022
The vulnerability affects the following Valmet DNA versions: Valmet DNA versions from Collection 2012 to Collection 2021
CVE-2021-26726
CVSS:3.1/AV:A/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:P/RL:U/RC:C/CR:H/IR:H/AR:H/MAV:A/MAC:L/MPR:N/MUI:N/MS:U/MC:H/MI:H/MA:H
8.8
The fix is available from Valmet Automation Customer Service
Valmet suggest to use a properly configured firewall to prevent unauthorized access from untrusted networks to the system.
Ivan Speziale of Nozomi Networks
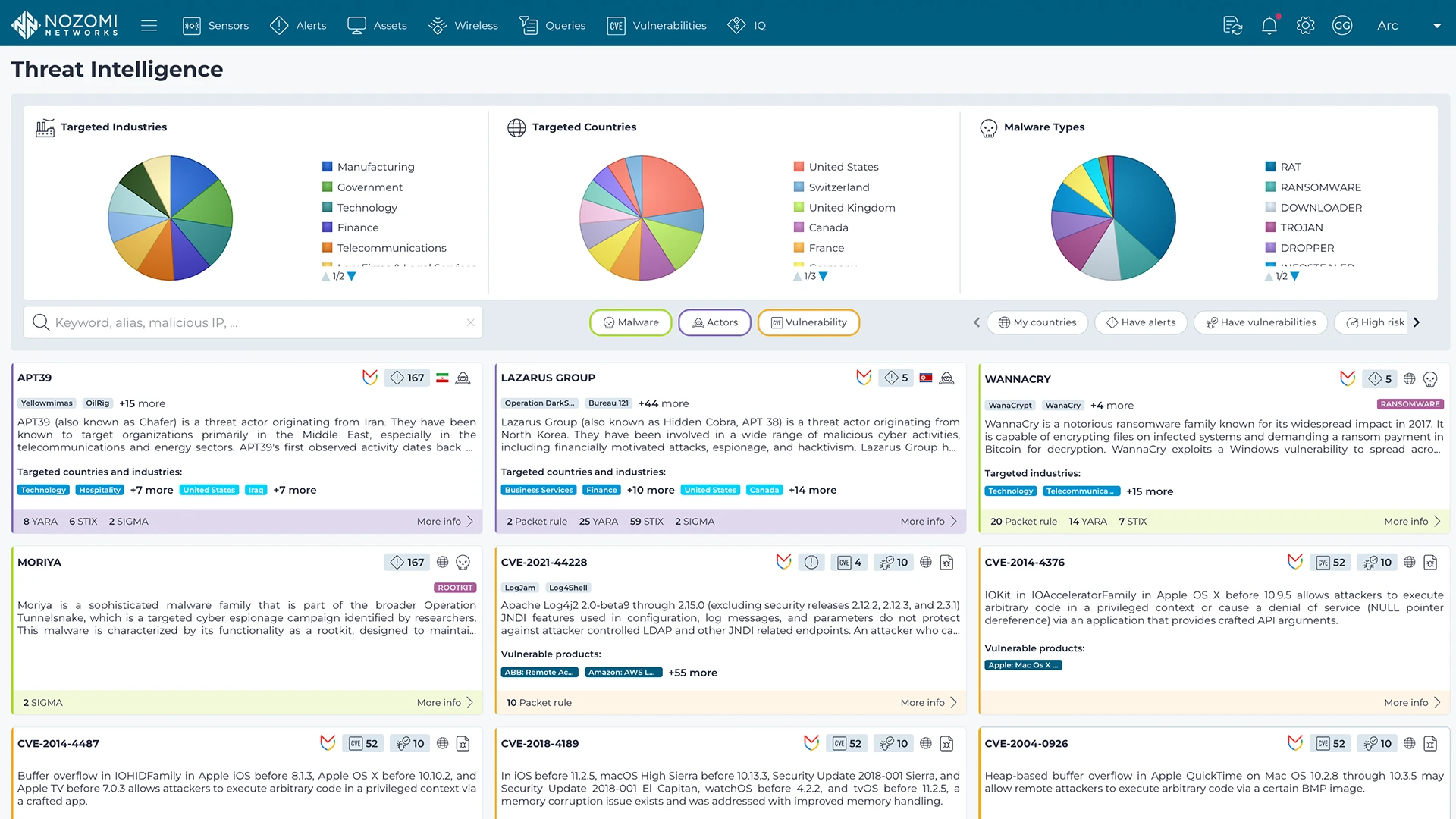
Nozomi Networks Labs curates threat and vulnerability insights that are continuously fed into the Nozomi Networks platform to ensure our sensors can detect existing and emerging threats and vulnerabilities that threaten customers environments.
Learn more